
Dummy Ip Address For Testing

what is a good invalid IP address to use for unit tests? – Stack …
I am writing unit tests for a client library. I want to test connecting with an invalid port and an invalid ip. What is a good ip address to use that won’t potentially be routed somewhere? I don’t want to make any assumptions about the network the machine running the unit tests is on. LOCALHOST seems like a bad choice since that is the valid machine running the server component and I want to test an invalid port separately. Is there an INVALID-IP reserved somewhere in the IPv4 spec?
asked May 4 ’12 at 20:57
0
According to RFC 5737:
The blocks 192. 0. 2. 0/24 (TEST-NET-1), 198. 51. 100. 0/24 (TEST-NET-2),
and 203. 113. 0/24 (TEST-NET-3) are provided for use in documentation.
This means you can use pick an IP address from these ranges:
192. 0 – 192. 255
198. 0 – 198. 255
203. 0 – 203. 255
answered May 4 ’12 at 20:59
JonathanJonathan6, 1501 gold badge27 silver badges44 bronze badges
6
If you’re looking for a truly invalid IP address (as opposed to an unrouteable one), you can take advantage of the fact that the first byte of a Class A address cannot be 0.
For example:
0. 42. 42
answered May 4 ’12 at 21:00
Frédéric HamidiFrédéric Hamidi244k40 gold badges460 silver badges465 bronze badges
4
The answer from Jonathan (and it’s comments) are good for IPv4
If your tests support IPv6 it has an explicit black hole you can use: 0100::/64 as defined in RFC 6666
It’s tempting to use 254. 254. 254 since it’s easy to remember, but on some platforms it gives a immediate “transmit failed. General Failure” rather than an actual timeout which may be an invalid unit test.
answered Apr 3 ’19 at 17:25
Chris RuddChris Rudd3013 silver badges5 bronze badges
1
There’s 3 private IP blocks you can use for such things:
10/8 (10. 0 -> 10. 255. 255) (an old school Class A netblock)
172. 16/12 (172. 16. 0 -> 172. 131. 255
196. 168/16 (192. 168. 0 -> 192. 255) (an old school Class B netblock)
Marc BMarc B344k39 gold badges387 silver badges471 bronze badges
254. 254
Should be in the reserved for future use domain…
RFC 1700
2
Not the answer you’re looking for? Browse other questions tagged unit-testing tcp ip or ask your own question.
How to Use a Fake IP Address and Mask Yourself Online
As the notion of privacy gets trampled on with each passing year, online privacy only becomes even more important.
That’s why many people use fake IP addresses. To be clear, “fake IP address” is a bit of a misnomer that implies creating a new one out of thin air. That’s not possible. The best you can do is hide your IP address behind someone else’s already-existing IP address. This is called IP masking. So how do you spoof your IP address?
1. Use a VPN
VPN stands for Virtual Private Network, but is much simpler than it sounds. Basically, you can connect your computer or device to someone else’s network, then browse the web through it. Whatever activity you’re doing looks like it’s coming from them, not from you.
When you connect to a VPN, you’re masking your IP address with one of the IP addresses on that network. To trace the traffic back to you, the VPN would have to give you up (or your IP address would have to be revealed via DNS leak).
For best results, use a paid VPN service because free VPNs come with too many risks and downsides. The most important one is that you can never quite trust a free service. Are they selling your data? If asked, would they give up your true IP address? It does happen.
As such, we only recommend using a logless VPN. Such VPNs don’t keep activity logs, so they can’t give up your IP address even if requested. Plus, most logless VPNs encrypt all of your traffic to and from the network, preventing any snooping by ISPs or governments.
VPNs are useful in so many circumstances, but there are too many myths about them that might put you off; you should dispense with misinformation and use a VPN for secure searching.
Which Is the Best VPN For You?
ExpressVPN and CyberGhost are both excellent options. If neither suits you, have a look at our overview of best VPN services. Long story short: whichever service you pick, you just download the app, run it, and use it to connect to the VPN on demand. It’s really that simple.
Use this link for up to 49% off ExpressVPN plans!
2. Use a Web Proxy
A web proxy works in much the same way as a VPN. You connect to the proxy server, then all your web traffic flows through the proxy server. As such, your IP address gets hidden by the proxy server’s IP address.
But there are two major differences between proxy and VPN.
Firstly, web proxies are typically unencrypted. Even if your IP address is masked by a proxy, the traffic itself can still be sniffed by ISPs and governments. Not only that, but some websites may still be able to see your real IP address using JavaScript and the now largely-defunct Flash, which are another set of threats to your online security.
Secondly, some browsers let you route only browser traffic. To use a web proxy, you go into your web browser’s settings and manually input the proxy server’s IP address. This allows applications and devices outside the web browser, like Skype, to still use your actual IP address.
Find a free web proxy using a site like PremProxy or Proxy List. Using a proxy server in your country will keep it fast, but using a proxy server in another country can be useful for bypassing region-blocked content and adding a tiny layer of extra obscurity.
How to Set Up a Web Proxy in Firefox
In the browser, select Preferences from the dropdown menu in the top-left corner.
In the General section, scroll down to Network Settings.
Click on Settings.
Select Manual proxy configuration, then type in the proxy’s address and port in the HTTP Proxy field.
How to Set Up a Web Proxy in Microsoft Edge
On the homepage, click on three dots from the top-left corner.
Select Settings.
Search for proxy in search settings, and selectOpen your computer’s proxy settings.
In the Settings window, toggle the Use a proxy server option, and type in the proxy’s address and port in the Address field.
Click on Save to finalize your proxy setup.
How to Set Up a Web Proxy in Chrome, Opera, Vivaldi
In the main menu, select Settings.
Under Network, click Change proxy settings…
In the Connections tab, click LAN settings.
Enable Use a proxy server for your LAN, then type in the proxy’s address and port in the Address field.
Note: Chrome, Opera, Vivaldi, and other Chromium-based browsers do not have a built-in browser-specific proxy feature. Instead, they only use system-wide proxy settings. However, you can use an extension like Proxy Switcher & Manager to use web proxies that only affect browser traffic.
3. Use Public Wi-Fi
Instead of routing your traffic through another person’s network, you can opt to connect directly to their network—and the easiest way to do this is to hop onto public Wi-Fi.
The funny thing is that this is really the only way to hide your home IP address. When you’re on public Wi-Fi, there’s no way for someone to trace it back to your home. And if it’s a popular hotspot (e. g. Starbucks), your activity will be obscured by dozens of other users at any time.
But remember that public Wi-Fi has its risks.
By default, most public Wi-Fi hotspots are unencrypted. All your activities while connected can be seen by anyone else on the network (if they’re sniffing it out), which includes login details for websites like banks and e-commerce shopping. Public Wi-Fi hotspots can also spread malware infections to your device.
On top of this, there are several other ways for hackers to steal your identity on public Wi-Fi. So while you might be hiding your IP address, you’re still opening yourself up to a whole host of other privacy and security risks.
4. Use Tor Browser
Tor browser, sometimes also called the Onion router, is a free browser that hides your IP address every time you connect to the internet. It does this by connecting you with the Tor network at the start, which transmits your data through random relay servers hosted by worldwide volunteers.
For most people not living in authoritarian countries like China, Venezuela, etc. (where Tor is banned), it’s a handy tool to have in your arsenal of privacy solutions.
To get started, go to the official Tor website and install the browser from there. When the setup is complete, click on Connect. The Tor browser will then link up to the Tor network. This could take a few minutes, so you’ll have to wait a short time.
When it’s done, you’re free to browse the internet anonymously. If you’re using Tor for the first time, though, make sure that you read up on all the online security tips about using Tor efficiently. They are given on the homepage itself!
And That’s How You Can Hide Your IP Address!
Now you know all the different ways you can mask your IP address. If you’re like us, and just can’t accept that “big brother” is prying on you all the time, these tricks will be enough to get started with securing your online anonymity.
Privacy vs. Anonymity vs. Security: Why They Don’t All Mean the Same ThingWhat’s the difference between security, anonymity, and privacy? And when should you prioritize one over another?
Read Next
About The Author
Joel Lee
(1521 Articles Published)
Joel Lee is the Editor in Chief of MakeUseOf since 2018. He has a B. S. in Computer Science and over nine years of professional writing and editing experience.
More
From Joel Lee
Subscribe to our newsletter
Join our newsletter for tech tips, reviews, free ebooks, and exclusive deals!
Click here to subscribe
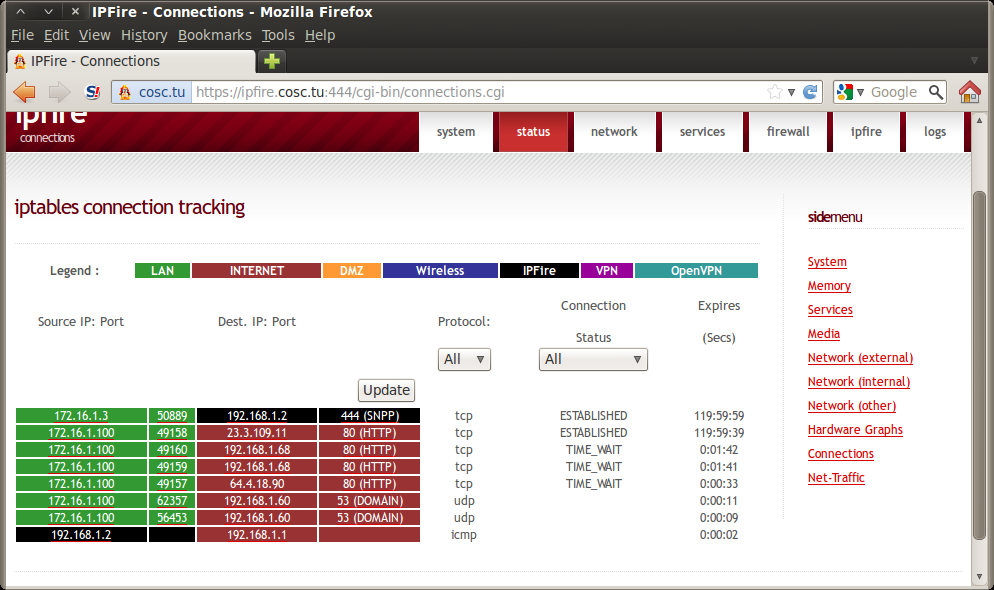
Using IP Spoofing to Simulate Requests from Different IP Addresses
It’s not easy today to find a single node system as both failover and resilience are key points of modern applications. So if you need to load test a system, it will likely be something clustered.
The idea of a cluster is to protect the application from failure. If one node goes out of order, the remaining ones will continue to serve incoming requests. Usually hardware or software load balancers act as a single entry point, orchestrating all the incoming requests and sending them to the appropriate backend servers.
We have already covered the situation when the load balancer has more than one IP address and we know how to configure JMeter to hit all the load balancer endpoints. If it is something you missed you’re very welcome to read The DNS Cache Manager: The Right Way To Test Load Balanced Apps guide.
One of the main features of load balancers is “stickiness” or “persistence” – a mechanism of wiring a client to one backend node behind the load balancer so requests could go back and forth. For example, if the application uses cookie-based authentication and the user has logged into one of the backend nodes, he will be authenticated there only for the amount of time required to replicate the session cache (which may be not immediate). This is one reason for stickiness.
As simulated by JMeter the request goes via the Load Balancer, hits Server A and gets a Cookie. If the following request will go to the Server B it will not be authenticated as for the moment only Server A knows about this user and accepts its Cookie unless local caches are replicated into a Shared Cache.
A similar situation will happen if a protocol other than HTTP is being used. If communication is being conducted via FTP, it is vital that the requests are going back and forth between JMeter and Server A within the bounds of one session.
Assuming all of the above is happening, you can run into a situation when all of the requests sent from JMeter are hitting only Server A, and Server B doesn’t receive any load. As a result, you cannot tell for sure whether or not your application is scaling correctly and the results of the load testing are vague. So let’s look at how to simulate requests originating from different IP addresses in your JMeter test.
If you look at the bottom of HTTP Request Sampler (you may have to scroll down) you’ll see the “Source Address” input.
You can use this input for IP Spoofing and put the IP address, hostname or network interface name so that JMeter will send the request from the specified source. Drop-down choices are:
IP/Hostname
Device
Device IPv4
Device IPv6
Usually load generator machines don’t have more than one network interface so I’ll focus on IP/Hostname bit. First of all we need to add a number of IP addresses on the operating system level.
For the Microsoft Windows family it can be done in 2 ways:
Depending on your Windows distribution look for “Network Connections” window in the Control Panel, right click on the interface and choose “Properties”.
Another option to reach this window is by pressing Win+R combination, typing and hitting Enter.
On the next window choose “Internet Protocol Version 4” and click “Properties” again.
Once you click, the following window will open:
Make sure that you uncheck “Obtain an IP address automatically” and set the IP address, netmask, gateway and DNS servers manually. In the case of a DHCP-assigned address, the IP alias feature won’t work and you won’t be able to add extra IP addresses to your network adapter.
Once you configured the manual IP address, click the “Advanced” button. It will take you to Advanced TCP/IP Settings configuration window where you can click the “Add” button and add as many IP addresses as necessary in addition to your main IP address.
As you can see, I’ve added the 10. 20. 30. 40 IP address. For the “255. 255. 0” netmask, it is possible to have 253 extra IP addresses (256 minus broadcast address minus network address minus primary IP) but in fact you’re only limited with your gateway configuration, RAM, test scenario details, and fantasy. Theoretically it should be possible to simulate as many as 4, 294, 967, 294 IP addresses with a single network interface. I didn’t experience any problems with something like 2000 IPs per interface.
A quicker and (in my opinion) better option is using the Windows Command Prompt and netsh add command so adding a single IP address is as simple as:
netsh interface ipv4 add address “Wi-Fi” 10. 40 255. 0
You can use Windows shell scripting to add the whole range of IP addresses in a single command as follows:
FOR /L%A IN (40, 1, 50) DO netsh interface ipv4 add address “Wi-Fi” 10. %A 255. 0
The above command will add 11 IPv4 addresses to the “Wi-Fi” interface starting from 10. 40 and ending with 10. 50 inclusively. I expect that it is more logically compliant to use ethernet for performance testing so your actual network interface name will be different so check it in the “Network Connections” window and replace my “Wi-Fi” with your actual network connection name.
(Linux and MacOSX systems support similar feature. To keep the post more IP Spoofing oriented, I will skip instructions for these systems, but if you need an exact command for your operating system and/or test scenario feel free to ask for it in the comments section in the bottom of this post, either myself or someone else will be happy to assist. )
Now let’s get back to JMeter.
For proof of concept, I’ll use Apache Tomcat which has some out-of-box web pages and capable of recording IP addresses of incoming requests in its access log. A very default deployment running on port 8080 is installed on my computer, so let’s hit Tomcat with a single HTTP Request and see how it goes.
Given the following JMeter configuration:
Thread Group with 1 thread and 1 loop
HTTP Request
Server name: localhost
Port Number: 8080
View Results Tree Listener
This is pretty much the default View Results Tree listener output containing sample start time, load time, body size, response headers, etc.
Now let’s look into Tomcat access log. It is located under /logs folder of Tomcat installation and default name looks like “localhost_access_log” + timestamp:
In the access log we can see
response body size (which is 11418 bytes)
response code (which is 200)
protocol (which is HTTP)
method (which is GET)
timestamp
and the most important bit: source IP address, which is currently 127. 0. 1
Now let’s try setting the IP address to the previously added one, i. e. 10. 40. In order to do it, it’s enough just to put the IP into “Source Address” input of the HTTP Request Sampler.
Now let’s look into the access log again.
Voila, origin IP address is now 10. 40
Now let’s go ahead and hit Tomcat server with 10 threads, each of them having different IP address. I will use CSV Data Set Config to read the IP addresses from the file.
Let’s put the IP addresses from 10. 41 to 10. 50 into a file like:
Add a CSV Data Set Config element to the test plan and configure it to read the file by providing full path to the file and arbitrary variable name, let it be IP.
Now let’s set thread number to 10:
and configure “Source Address” to be ${IP} dynamic variable.
Now let’s run our test once again and see how it goes.
As it can be seen from the access log all the requests were sent at approximately the same time and each thread was using its own IP address. Mission completed.
In regards to running tests in the BlazeMeter Cloud you shouldn’t worry about IP Spoofing too much as BlazeMeter systems are distributed by design. Furthermore, you have an option of setting an arbitrary number of JMeter Engines to kick off.
Even more, you can control the hosts file of Blazemeter servers, it is quite enough to provide the file called along with your script and any other files and it will be automatically picked up.
Hopefully, this guide will make your life easier. As usual, if anything remains unclear you’re very welcome to ask questions or share any form of feedback via discussion section below.
For experienced JMeter users, you’ll want to view the on-demand webcast, How to Create Advanced Load Testing Scenarios with JMeter.
If you are new to JMeter, and you’d like to learn more, please sign up for our free online JMeter training course.
Be sure to read through all our JMeter list of resources!
To try out BlazeMeter and get more from your JMX script, request a demo, or out your URL in the box below and your test will start in minutes.
Frequently Asked Questions about dummy ip address for testing
What is an IP address for dummies?
An IP address is assigned to every computer on an Ethernet network. Like the street address for your home, an IP address identifies network computers. It helps traffic flow between computers because each one has its own IP address. Each value ranges from 0 through 255.
How can I make a fake IP address?
How to Use a Fake IP Address and Mask Yourself OnlineUse a VPN. VPN stands for Virtual Private Network, but is much simpler than it sounds. … Use a Web Proxy. A web proxy works in much the same way as a VPN. … Use Public Wi-Fi. … Use Tor Browser.Jun 9, 2021
Can you simulate an IP address?
Theoretically it should be possible to simulate as many as 4,294,967,294 IP addresses with a single network interface.Jun 9, 2015


