Search Proxies
How Google know I using elite anonymous proxy – Stack Overflow
My bot use webrequest to post to website that have reCaptcha.
If bot request without proxy, Google reCaptcha will MOST return a somehow readable image.
If bot request with anonymous proxy, and Google reCaptcha will ALL return double blob reCaptcha in which there are 2 black circle block which is extremely hard to recognized by even human.
So is that possible Google know a bot use elite anonymous proxy to request without any javascript running?
any possible way you can think? As I know, it is not possible because HTTP limit?
edit: if you access by vpn, google will not know it.
asked Oct 19 ’14 at 2:22
3
Google actively looks out for proxies/socks servers & adds them to some kind of black list.
The proxy servers you are using are not new,
others have used them for bots & other things long before you, that’s why Google knows when you are hitting the reCaptcha with a proxy.
As for VPN services Google knows about them as well,
the only VPN that Google would not know about is a VPN that you setup on a server that you own or a friend owns but after time of doing bad things Google will flag that IP as well.
When will you n00bs learn that Google is the all seeing eye, that knows all.
Your options are:. 1 make a new proxy servers (one way or another) who’s IP is not flagged.. 2 use hacked WiFi or use Free WiFi around your area.. 3 be carful when doing this but use your own IP address until Google flags it & then when they do flag it change your ISP IP by using your router mac address spoofer. (Note most ISP-routers will not have “mac address spoofer” most store bought router will have it)
Unplug your cable modem, set a new mac address on the WAN side of your router & then plugin your cable modem & you will have a new IP but your ISP may get pissed if you do it too many times.
I sure hope your not spamming websites, I’m not for spamming peoples websites. I use bots to brute force logins just to say I got in but that’s it;)
answered Oct 21 ’14 at 16:40
1
Not the answer you’re looking for? Browse other questions tagged javascript proxy recaptcha or ask your own question.
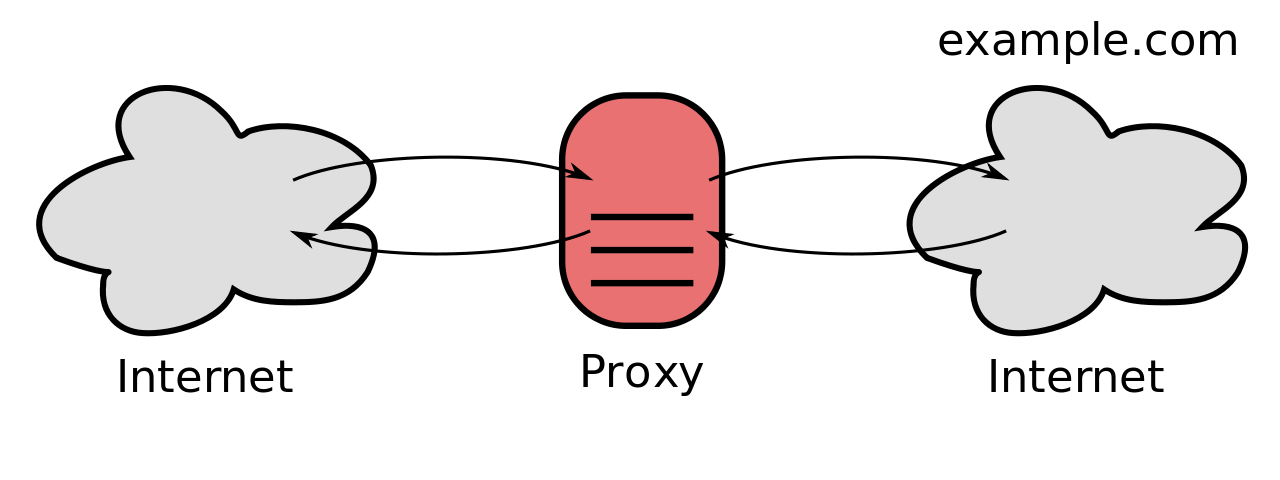
What are proxies and how can we detect them? – ipdata
Proxies come in many different shapes and sizes, some of them are easy to detect, others much harder. Some are used for illegitimate purposes, others are used as standard practise by corporations. In this post, we’ll explore the different types of proxies, what they can be used for, and how to detect them. A proxy is a simple server which forwards requests on your behalf. For example, if you’re using a proxy to access, your request will first be sent to the proxy server, which will then in turn make the actual request to, and return the result back to help explain it, let’s look at a simplified diagram of how your computer connects to a here’s how a proxy fits in…How is a proxy different from a VPN? This all looks very similar to a VPN, as we explored in our Tor Detection post, but there are some key you connect to a VPN, it establishes a secure, encrypted connection between your computer and the Internet. Your computer is connected to a remote and Virtual Private Network, so all Internet traffic will be sent over this connection, regardless of whether it’s from your web browser, a native application, or even your operating system checking for updates. Because of this, the VPNs are much heavier and have the potential to add more latency to your traffic. However, they’re more fully-functioning and generally more affic from VPNs can look identical to proxy traffic, so from a detection perspective there’s no difference – the IP address of the VPN or proxy can be looked up against a database or service, such as term “proxy” covers any server that forwards data on behalf of another user or server. Due to the broad coverage, there are many different types and styles of proxies, but most of these will use either HTTP or SOCKS as an underlying ProxiesAn HTTP proxy is one of the simplest types, and can be written in just a few lines of code. In, the module node–proxy makes the process very Proxy = require(‘-proxy’);
eateProxyServer({ target:”})(8000);
Now, if we run this, any requests to port 8000 will be forwarded on to and look as if they originated from the server where this is ProxiesA SOCKS proxy runs at a lower-level than a HTTP proxy, making it far more versatile. SOCKS can forward TCP and UDP connections and is therefore more commonly used than HTTP proxies. A SOCKS proxy can also be run over SSH using OpenSSH, allowing users to securely connect to is a system which effectively links multiple SOCKS proxies together to provide strong anonymity, at the cost of speed and some convenience. Read more about Tor detection of these proxy types can use any of the proxy technologies, such as SOCKS. A proxy can also fall into multiple categories! Transparent proxies simply pass on the request from the user to the destination, without making any modifications at all. Non-transparent proxies make some modification to the request, such as adding HTTP headers. Some proxies add an [x-forwarded-for]() header which includes the original IP address of the user, this would be an example of a non-transparent proxies are simply proxies which are accessibly by anyone on the internet, sometimes by mistake. Due to their open nature, they’re often used to provide anonymity and are frequently used for malicious activity. Using open proxies is extremely dangerous, unless you totally trust the proxy service you’re connecting to, as they may be snooping on all your internet rporate proxies are proxies run by corporations, usually hosted on their own servers. Many companies use proxies to control access to the internet and their networks from their ivate proxies are very similar to open proxies, but they require some kind of registration and usually promise to be more secure than open ’d be impossible to detect all proxy servers, but some can be detected. Proxy providers continually change their IP addresses to try to avoid are multiple lists of known proxy IP addresses available online, and ipdata combines many of them, along with proprietary lists to detect the larger ditionally, proxies are reasonably likely to be hosted by a cloud hosting provider, such as AWS or OVH. Traffic from hosting providers can usually be detected using the IP address, but of course there are sometimes legitimate reasons for a hosting provider to be calling your service – especially if you’re running an ’s an example ipdata response for a proxy:curl
{
ip: “54. 39. 133. 108”,
is_eu: false,
city: null,
region: null,
region_code: null,
country_name: “Canada”,
country_code: “CA”,
continent_name: “North America”,
continent_code: “NA”,
latitude: 43. 6319,
longitude: -79. 3716,
postal: null,
calling_code: “1”,
flag: “,
emoji_flag: ” “,
emoji_unicode: “U+1F1E8 U+1F1E6”,
asn: {
asn: “AS16276”,
name: “OVH SAS”,
domain: “”,
route: “54. 0. 0/16”,
type: “hosting”},
languages: [
name: “English”,
native: “English”},
name: “French”,
native: “Français”}],
currency: {
name: “Canadian Dollar”,
code: “CAD”,
symbol: “CA$”,
native: “$”,
plural: “Canadian dollars”},
time_zone: {
name: “America/Toronto”,
abbr: “EDT”,
offset: “-0400”,
is_dst: true,
current_time: “2020-09-04T12:42:43. 132643-04:00”},
threat: {
is_tor: false,
is_proxy: false,
is_anonymous: false,
is_known_attacker: false,
is_known_abuser: false,
is_threat: false,
is_bogon: false}}
Here, we can see ipdata hasn’t currently got this IP address on a known proxy list (_proxy), but the request is coming from a hosting provider (). Blocking proxiesDue to the difficulty in reliably detecting proxies, it’s usually not worth spending much time trying to block proxies. However, some proxies will be caught by _proxy and generally, ipdata will help protect your site from threats if you block all requests where _threat == are also many, totally legitimate, use-cases for proxies. Corporate proxies are common and blocking legitimate traffic from these companies could be costly!

Find Proxy Settings on Your Computer (for Local Testing …
We use cookies to enhance user experience, analyze site usage, and assist in our marketing efforts. By continuing to browse
or closing this banner, you acknowledge that you have read and agree to our Cookie Policy,
Privacy Policy and Terms of Service.
You can find the proxy settings applicable to your machine and use them to set up Local Testing connections.
Introduction
A proxy server sits between your machine and your ISP. In most organizations, proxies are configured
by network admins to filter and/or monitor inbound and outbound web traffic from employee computers.
In this article, we’ll show you how to view proxy settings (if your computer is behind a proxy server).
You can then use the information to set up Local Testing connections with BrowserStack..
Find Proxy Settings in Windows
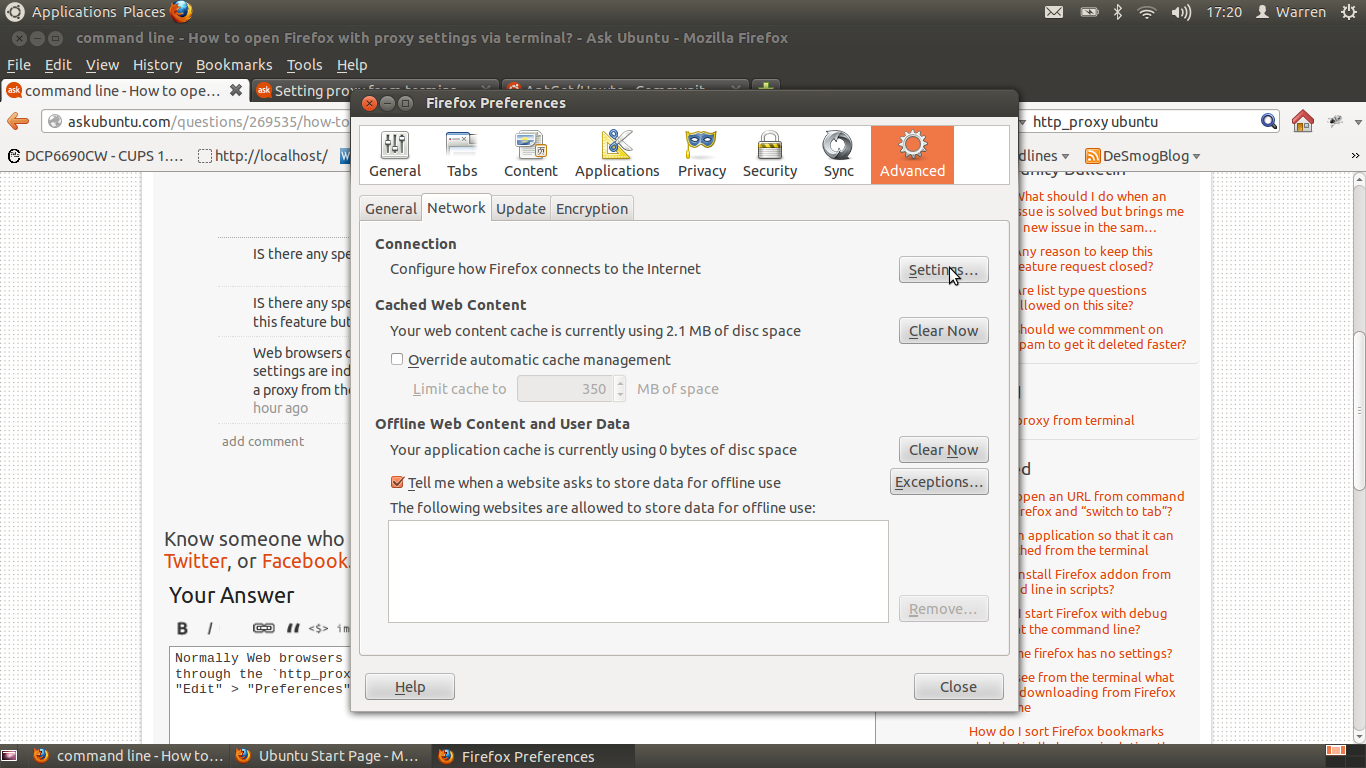
In most cases, browsers will use proxy settings that are set on the computer. However, each browser has a
settings page to configure proxy settings as well.
There are two ways to find proxy settings in Windows: via the Settings app (Windows 10 only) or via the
Control Panel.
Using the Settings App (Windows 10) to find proxy settings
Click on Start, then click on the gear icon (Settings) at the far left.
In the Windows Settings menu, click on Network & Internet.
In the left pane, click on Proxy.
Here you have all the settings that are related to setting up a proxy in Windows. It’s split into
two configurations: Automatic or Manual proxy setup.
Using the configuration details to set up Local Testing connection:
If “Use setup script“ is enabled, it means that you have configured PAC proxy on your system. You
can obtain the path to PAC file from the “Script Address“ section.
Note: To set up a Local Testing connection using the PAC file, you need to ensure that the PAC file is stored on your computer and path needs to an absolute path to that file.
If “Manual proxy setup” is enabled, you can simply obtain Proxy Host and Port from the “Address“
and “Port“ section.
For Local Testing to work correctly, you need to bypass the traffic for – – from your
proxy. You can do this by adding an entry in the Proxy Exception> text field in the
“Manual proxy setup” section.
Using Control Panel (all Windows versions) to find proxy settings
In any Windows version, you can find the proxy settings via the Control Panel on your computer.
Click on Start and open the Control Panel. Then click on
Internet Options.
In the Internet Options, go to Connections > LAN settings.
Here you have all the settings that are related to setting up a proxy in Windows. It’s basically
split into two configurations: either Automatic configuration or
Proxy Server setup.
If “Use automatic configuration script“ iis checked, it means that you have configured PAC proxy
in your system. You can obtain the path to PAC file from the “Script Address“ section.
If “Use a proxy server for your LAN” is checked, you can obtain Proxy Host and Port from the
“Address“ and “Port“ section.
proxy. You can do this by clicking the “Advanced“ button and adding an entry in the
“Do not use proxy server for addresses beginning with:“ text field.
Find Proxy Settings in OS X
On OS X, you have to view the proxy settings in System Preferences. This is where most browsers check automatically. However, each browser has a settings page to configure proxy settings as well.
Open System Preferences and click on Network.
On the left-hand side, click on an active network connection. Note that you can have different proxy settings for different network connections. Click on the Advanced button on the bottom right.
Click on the Proxies tab and you’ll see a list of proxy protocols you can configure.
If “Automatic Proxy Configuration“ is checked, it means that you have configured PAC proxy in your system. You can obtain the path to PAC file from the “Script Address“ section.
If “Web Proxy (HTTP)” or “Secure Web Proxy (HTTPS)“ is checked, you can simply obtain Proxy Host, Port, Username, and Password.
For Local Testing to work correctly, you need to bypass the traffic for – – from your proxy. You can do this by adding an entry in the ”Bypass proxy settings for these Hosts & Domains” text field.
Connection duration and disconnection
In Linux, finding your proxy settings will depend on what distribution you are running. Mostly, the procedure would be similar for the various distributions.
On Ubuntu, open on System Settings from the launcher and scroll down to Hardware. Click on Network.
Click on Network Proxy, you can choose from Automatic or Manual.
If the “Automatic“ option is selected, it means that you have configured PAC proxy in your system. You can obtain the path to PAC file from the “Configuration URL“ section.
If the “Manual“ option is selected, you can simply obtain Proxy Host and Port from the appropriate section.
For Local Testing to work correctly, you need to bypass the traffic for – – from your proxy. You can do this by using the command-line interface as follows:
To change proxy exceptions, use ‘set’ option with ‘gsettings’ command as follows.
$ gsettings set ignore-hosts “[‘localhost’, ”, ‘::1’]”
If access to the above sections is restricted on your computer, you can seek help from your IT/Network Team to gather this information.
Frequently Asked Questions about search proxies
Can Google detect proxies?
1 Answer. Google actively looks out for proxies/socks servers & adds them to some kind of black list. The proxy servers you are using are not new, others have used them for bots & other things long before you, that’s why Google knows when you are hitting the reCaptcha with a proxy.Oct 21, 2014
Can proxies be detected?
It’d be impossible to detect all proxy servers, but some can be detected. Proxy providers continually change their IP addresses to try to avoid detection. There are multiple lists of known proxy IP addresses available online, and ipdata combines many of them, along with proprietary lists to detect the larger proxies.Sep 14, 2020
How do I find my proxy location?
Find Proxy Settings in WindowsClick on Start, then click on the gear icon (Settings) at the far left.In the Windows Settings menu, click on Network & Internet.In the left pane, click on Proxy.Here you have all the settings that are related to setting up a proxy in Windows.