Is Getting Someone’S Ip Illegal
Is IP Grabbing Illegal? (All Questions Answered) – SmartyDNS
Your IP address is how you communicate with the Internet. Without it, that wouldn’t be possible.
Since it’s so important, you have to wonder – is IP grabbing illegal? Is it illegal to track an IP address?
We’ll answer those questions (and more) in this quick five-minute article.
Is IP Grabbing Illegal – Yes or No?
First, what is IP grabbing?
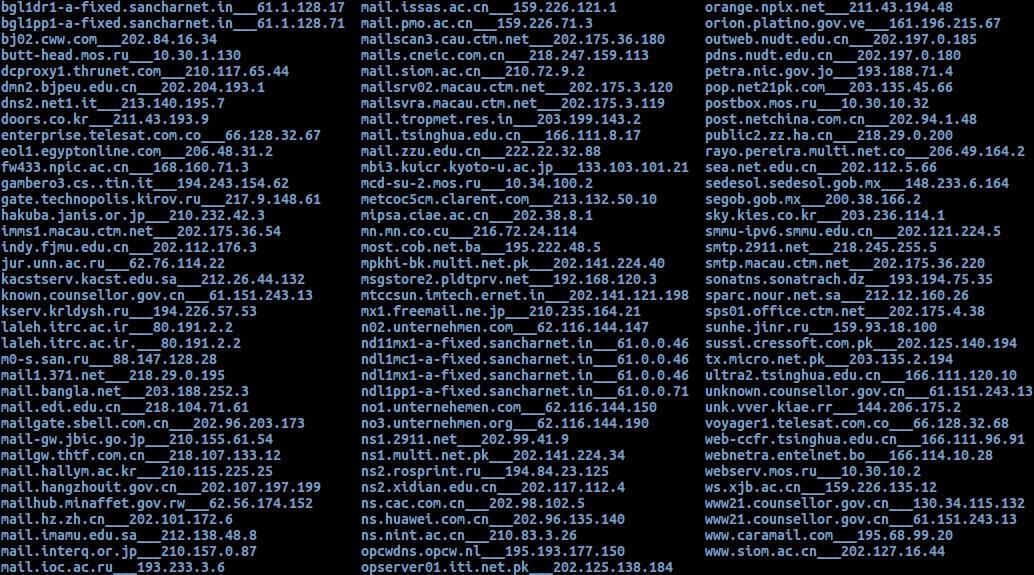
Well, it’s when someone uses a third-party service to “grab” your IP address. For example, they might use Grabify. It lets them create a link which they can send to you. If you access it, they’ll be able to see your IP address (alongside other information) on their end, like this:
If they click “More Info” on the right, they can even see your local IP address – the one your device uses on your network.
So is IP grabbing illegal?
Nope. There’s no specific law preventing someone from targeting you with an IP grabbing tool. Your IP address is pretty much public information at this point – just like your street address or phone number.
However, what someone does with your IP address can become illegal.
Here’s When IP Grabbing Is Against the Law
When the person grabbing it decides to DDoS you (basically, force you offline with cyber attacks). They can target your network with a DDoS attack because they know your IP address. In most places, doing this is illegal. DoS attacks, however, might not always be illegal because they’re weaker than DDoS attacks. If someone targets you with them constantly, though, you can contact the the person who grabbed your IP address tries using it to remotely hack your computer. Normally, an IP address isn’t enough to do that, but some skilled hackers could abuse Shared Resources to perform such a cyber attack. They could also use it to scan for open ports, which they then try to exploit to take over your someone uses IP grabbing to target you with phishing attacks. For example, they use it to find who your ISP is, and then they target them with phishing and vishing attacks.
Is IP Tracking Illegal?
It sounds like it should be, but it normally isn’t. It’s how websites keep track of their users, and how they display ads on the Internet. Businesses also use it for all sorts of B2B purposes (marketing, delivering services, analytics, etc. ).
As long as they meet any legal data processing requirements (like the GDPR), there are no conflicts with the law.
Is It Illegal for an Individual to Track Your IP Address?
Again, not really. They can freely use services like IP Logger or IP Tracker to keep tabs on your IP address. There’s no specific law against that.
But if they track your IP address for illegal purposes (harassment, stalking, DDoS-ing, cyber attacks, etc. ), it obviously goes against the law.
Should You Hide Your IP Address?
That’s up to you.
If you want to enjoy more privacy, and not have websites and random people track it, you should definitely do it. The same goes if you don’t want hackers abusing it or using it to DDoS you.
Plus, you get to enjoy other perks if you hide your IP address:
The ability to prevent anyone from finding out what country and city you are from + who your ISP is and what your ZIP code can bypass geo-restrictions and unblock different websites and online services – like Netflix or Pandora can also bypass firewalls at work and school. Also, you can get around government censorship since it also relies on firewalls to block hiding your IP address, you make it much harder for advertisers to track your online movements and spam you with personalized might be able to bypass geographical price discrimination. That’s when sites display different prices based on your geo-location. Hiding your IP address means websites won’t be able to see your geo-location rrenting becomes safer because wannabe hackers, lawyers, and copyright trolls can’t see your IP address in the swarm risk of a cybercriminal logging it and selling it on the dark bans won’t stop you from gaming online or posting on forums.
How Can You Hide Your IP Address?
These are the most convenient ways to do it:
1. Use a VPN
This is an online service that masks your IP address and encrypts your traffic. Here’s how the process works:
You download and install a VPN app on your use the app to connect to a VPN app and the server establish a secure connection between data that passes through that connection is encrypted end-to-end (only the client and server can encrypt/decrypt it) you visit a website, your connection requests go to it through the VPN website receives the requests from the VPN server, so it only sees the server’s IP else who tries looking up your IP address will also only see the server’s address.
Overall, a VPN is a great way to protect your privacy. Plus, by encrypting your traffic, it makes sure that:
Hackers can’t abuse vulnerable WiFi networks to monitor your and surveillance agencies can’t spy on your online can’t throttle your bandwidth anymore.
Looking for a reliable VPN service?
Here at SmartyDNS we offer high-speed VPN servers with military grade 256-bit AES encryption and highly secure VPN protocols (OpenVPN, SoftEther and IKEv2), and we we adhere to a strict no-log policy.
Our VPN servers act as proxy servers and we also offer Smart DNS service that allows you to unblock 300+ geo-restricted websites around the world.
We offer convenient VPN apps for Windows, Mac, iPhone / iPad, Android and Fire TV / Stick, and extensions for Chrome and Firefox browsers.
Special offer! Get SmartyDNS for $ 2. 9 per month!
Yes, and we’ll also get your 30-day money-back guarantee.
Сэкономьте 63% сейчас
2. Use a Proxy
A proxy server works similar to a VPN – it intercepts your connection requests to the web, and forwards them on your behalf. So any site you visit will only see the proxy server’s IP address.
However, unlike a VPN, proxies don’t offer powerful encryption. Sometimes, they don’t offer any at all.
So you get some privacy by hiding your IP address, but your traffic might not be secure. Also, if you use a free proxy that’s run by a malicious actor, they could log your data.
Generally, you should only use a proxy if you need to unblock a web page. If you need security on top of that, use a VPN. Instead of getting separate services, consider using a VPN whose servers double as proxies. It’s much cheaper.
3. Use Mobile Data or Switch WiFi Networks
If you’re on your mobile and want to change your IP address realf fast, try switching from WiFi data to mobile data.
You’ll use your mobile provider’s network instead of your WiFi network’s ISP, so you’ll get a different IP address.
What if you have a limited mobile data plan and normally use WiFi, though?
In that case, you can switch WiFi networks to change your IP address.
4. Ask Your ISP to Change It
They assigned you your current IP address, so you can ask them to change it. Maybe see if they can offer a dynamic IP address too (one that changes at regular intervals).
If you already have a dynamic IP address, you can usually change it by restarting your router.
Can You Hide Your IP Address with Tor?
Yes, you can do that. Just like a VPN, your connections will go to the Internet through a server. So everybody will see the IP address of the Tor server you’re using.
But we have to warn you – Tor has had and continues to have issues with IP leaks:
In 2017, the TorMoil issue leaked users’ IP might leak your IP address when you try to open Windows DRM rrent clients can sometimes leak your IP address. Certain file types (like PDFs) can bypass proxy settings, causing Tor to leak your IP address.
Besides that, you’ll also get pretty slow speeds because there are only around 6, 000 servers for over two million users.
Is IP Grabbing Illegal? The Bottom Line
Not unless the person grabbing your IP address wants to use it to do something illegal – like DDoS-ing you or hacking into your computer.
For normal purposes, IP grabbing (and tracking) is generally legal. If you’re worried it violates your privacy, use a VPN to hide your IP address. It’s the easiest and most convenient way to do it. If you know other methods to mask your IP address (other than the ones we already mentioned), go ahead and tell us about them in the comments.
Technology vector created by freepik –
In California, and the US, can you trace someone’s IP legally?
IANAL, but I am a computer formation on the internet is sent in the form of packets. The most common is IPv4 ammended with a couple of cool IPv6 tricks. They look like this. Points of interest here:-All packets have a header-All headers have a source IP and destination IPKind of like a letter. So if you send me a packet directly from you computer then you have directly sent me all the above information, plus whatever the actual content of the packet is (doesn’t matter for this purpose). So “tracing their IP address” is akin to reading the return address on a letter. It’s freely available information that’s not hard to find. At most games will act as an in between, where everyone sends packets to the game server, and the server sends updated info to everyone. However, in some games, and in many forms of internet communication, packets are sent directly between two if you’re friend is bragging about being able to get someone’s IP address just to show how big his e-pen is, don’t worry about it. If he decides to use that information to commit a crime, then you can come as a computer guy who knows the kind of crimes you can commit using an IP, and know that these f-ers are almost never punished, if your friend starts talking about DDOSing, please punch him in the dick for me.
Is DDoSing Illegal? | UpGuard
You’re woken by your phone erupting with notifications. You drowsily reach for it and find a barrage of messages from frustrated clients complaining about your try to load your website but you’re met with a frightful “service unavailable” could be a victim of a DDoS is a DDoS attack? A Distributed Denial of Service attack (DDoS attack) is the process of sending an overwhelming amount of data requests to a web server with the intention of impeding its performance. This disturbance could cause the web server to slow down or completely DDoSing Illegal? Whether your seeking vengeance for poor customer service or you just want to play a practical joke on a friend, launching a DDoS attack against another person or business is DDoSing Illegal in the U. S? DDoSing is an Illegal cybercrime in the United States. A DDoS attack could be classified as a federal criminal offense under the Computer Fraud and Abuse Act (CFAA). The use of booter services and stressers also violates this you’re found guilty of causing intentional harm to a computer or server in a DDoS attack, you could be charged with a prison sentence of up to 10 you believe you are a victim of a DDoS attack you should seek legal advice as soon as Does a DDoS Attack Work? A DDoS attack is a coordinated attack between multiple computers and internet of things (IoT) devices. These devices are infected with malware so that they can be controlled by cyber more infected devices (bots) an attacker recruits, the more powerful the assault. When these bots are linked together the malicious network is known as a botnet. A botnet is comprised of multiple compromised devicesWhen a DDoS attack is initiated, each bot sends consistent traffic requests to the host IP address. This flood of requests overwhelms the web server forcing it to deny entry (or deny service) to legitimate website ‘s a fascinating visualization of a DDoS attack in action:DDoS attacks are not always launched for extortion purposes, like ransomware. They’re usually intended to solely cause disruption and send a message of hatred. They can be launched either by an individual or a group of motivation behind a DDoS attack ranges from personal vendettas to political activism. Some attacks are launched by hacktivist groups, such as the ubiquitous group Types of DDoS Attacks There are many variations of DDoS attacks. Some are simplistic and fairly easy to mitigate, others are deeply complex. To maximize damage and frustration, attackers sometimes use a variation of DDoS attacks in a single event. Here are three common types of DDoS attacks. 1. Volumetric attacksThis is the most common type of DDoS attack. The attacker floods a web server with data packets to completely saturate its bandwidth. This prevents real visitors from loading a victim’s website. DNS amplification is a type of volumetric attack where amplified data requests are made to open DNS servers and the resulting response traffic aimed at victims. 2. Application attacksIn an application attack, the very top layer of the Open Systems Interconnection (OSI) model is targeted, layer 7. Because application attacks are focused on just the top layer, they require less bandwidth saturation to execute a successful DDoS application attacks target the path of common internet requests, such as HTTP, these attacks could request millions of downloads per second or millions of page refreshes per second. The effect is a rapid consumption of server resources. 3. Protocol attacksThis particular cyber attack target levels 3 and 4 of the OSI model. It aims to deplete server resources for firewalls and load example of a protocol attack is a SYN flood attack. A SYN flood attack exploits the standard 3-way handshake of a TCP/IP transaction. The three-phase of this transaction are as follows:SYN – the host receives a message to initiate the transactionSYN/ACK – confirms the request for informationACK – server closes the a SYN flood attack, the server sends an ACK message to a spoof IP address that doesn’t respond, preventing the handshake loop from closing. Because the server is forced to wait for multiple ACK responses that never arrive, its resources are ‘s the Difference Between a DoS Attack and a DDoS Attack? A DoS attack is executed by a single computer whereas a DDoS attack is executed by a network of compromised devices. The cumulative effect of DDoS attacks makes them substantially more destructive to web servers. Difference between a DoS and DDoS attackDDoS attacks are severely detrimental to an online business because they completely stop the flow of traffic or slow a website down to the point of it being unusable. In both scenarios, a website’s income generation engine will grind to a owners need to, therefore, learn how to identify when a DDoS attack is taking place and understand the correct remediation to Identify When a DDoS Attack is HappeningThere are a couple of signs that may be evidence of a DDoS attack taking place. These signs alone are not enough to conclude an attack is taking place, but they should encourage further investigation. 1. Your website is loading very slowlyBecause DDoS attacks deplete the resources of web servers, a website under attack will process information very slowly if it can still be loaded. You can test your site speed for free using Google’s page speed insights tool. You should have a benchmark site speed value to measure ensure there isn’t an issue with your internet connection, you should try to load other websites too. You receive a 503 service unavailable error If you see a ‘503 service unavailable error’ when you try to load any of your webpages, but other websites load perfectly, there’s a high chance you’re a victim of a DDoS attack. The 503 service unavailable error means that a web server is incapable of processing a load request. Keep in mind that this error could also mean that a server is temporarily down for maintenance. A 503 error should definitely warrant further investigation. If you don’t have access to your server logs, you should contact your ISP to check the status of your server. If you do have access to your web server, you can identify a DDoS attack from access entifying a DDoS Attack from the Command Line Interface (CLI)Through your web server’s Command Line Interface (CLI) you can generate a log of all the active connections to your can generate a list of the IP addresses connected to your server ports with the following command prompt:netstat -anHere’s an example output:Healthy web server log example – source: mDuring a DDoS attack, you will notice multiple instances of the same IP address connected to one server port, timing out the ‘s an example of such an instance:Example of web server log during DDoS attack – source: can narrow your filter to only list HTTP requests for your website on port 80. This will help you identify multiple connections from a single IP address. To do this use the following command:netstat -an | grep:80 | sortTo list the number of connections by IP address to port 80 (HTTP traffic), use the following command:netstat -plan|grep:80|awk {‘print $5’}|cut -d: -f 1|sort|uniq -c|sort -nk 1You should also analyze IP address connections on the port running all encrypted traffic (HTTPS), port tstat -an | grep:443 | sortAnd list the number of connections by IP address to this encryption port as follows:netstat -plan|grep:443|awk {‘print $5’}|cut -d: -f 1|sort|uniq -c|sort -nk 1To see how many times each IP address connects to your server, use the following command line:netstat -ntu | awk ‘{print $5}’ | cut -d: -f1 | sort | uniq -c | sort -nDuring a DDoS attack, your server may receive thousands of connection requests from a single IP address, so look for unusually high server requests. In 2014, CCTV cameras infected with malware were used to launch a DDoS attack peaking at 20, 000 requests per second (RPS). Similarly, in 2016 a devastating Mirai-based DDoS attack was launched against Dyn, a DNS service company. The attackers used Wi-Fi cameras in their botnet to implement the attack. The attack resulted in internet outages throughout most of the east most effectively identify a DDoS attack from your server logs, you need to have a server connection activity baseline to measure against. This will help you identify and resolve an attack as soon as possible instead of waiting to see how the data to Do During a DDoS AttackIf you don’t have immediate access to your web server, you should contact your internet service provider as soon as possible. Once the attack has been resolved, they may provide you with a new IP address. To save you time (and stress) during a DDoS attack, preemptively call your internet service provider to note down the direct number to call when one is taking place. Like all cybersecurity threats, a speedy response is you do have access to your server, you should clear your logs ASAP. Because the aim of DDoS attack is to deplete as many of your web resources as possible, your web server could fail catastrophically under the immense data load. Make sure you are only clearing log data you do not you can identify suspicious IP addresses during a DDoS attack, you should blacklist them and monitor the progression of the attack. If the severity is decreases or the IP addresses attempt to connect again, they’re likely from innocent visitors. DDoS attackers tend to modify the IP addresses of their botnets in response to being to Prevent DDoS Attacks DDoS attackers are continuously evolving their strategies to bypass mitigation solutions. Their methods continue to grow in complexity and severity. To give your business the highest chances of fending off a DDoS attack you need to implement several cybersecurity defense layers. Increase the bandwidth of your web serverWith a broader resource bandwidth, your server could possibly bear the burden of a DDoS attack while keeping your website functioning. In-house server hardware does not give you the option of efficiently expanding your bandwidth to meet increased demand. This limitation makes on-premise hardware vulnerable to failure during a DDoS might want to consider switching to a secure cloud-based web server. Advanced Cloud-based web servers let you expand your bandwidth very efficiently. They also offer a bandwidth tolerance to absorb DDoS attacks before your resources are cloud-based servers have a dedicated security team continuously monitoring your website for DDoS attacks. Blacklist suspicious IP addressesIf you identify suspicious IP addresses accessing your website you should blacklist them. This would require you to continuously monitor your access logs for unusual activity. Just make sure you’re not too trigger happy, you don’t want to blacklist innocent prospective customers. Implement multiple firewalls with packet filtersMultiple firewall layers are a very effective DDoS protection solution. In a double firewall setup, traffic needs to pass through two screening routers and a Bastion host before entering your internal first filter identifies and removes spoofed source IP packets. Spoofed packets are identified when their hop count values differ from the original source IP second filter has stricter entry conditions. It uses a Router Path Analysis (R-PA) method to analyze the path names of the entering data packets. Spoofed IP packets can be readily identified by their path name values and FIrewall DDoS DefenceCan a VPN Defend Against DDoS Attacks? A VPN cannot protect you from a DDoS attack if the attacker knows your real IP address. If you think a potential attacker knows your IP address, you should change it to reap the cybersecurity benefits of your your internet service provider offers you a dynamic IP address, resetting your router will modify your IP address. Otherwise, you will need to contact your ISP to have it manually Your Business at Risk of a Data Breach? At UpGuard, we can protect your business from data breaches, identify all of your data leaks, and help you continuously monitor the security posture of all your your risk of suffering a data breach, CLICK HERE to get your FREE security rating now!
Frequently Asked Questions about is getting someone’s ip illegal
Is tracing an IP illegal?
It’s not illegal to trace an IP. It’s very easy and there’s hundreds of websites that do it. He can trace people’s IP on online games because a lot of time the VOIP service they use is unencrypted or doesn’t hide the IP.Apr 13, 2016
Is DDoSing a friend illegal?
DDoSing is an Illegal cybercrime in the United States. A DDoS attack could be classified as a federal criminal offense under the Computer Fraud and Abuse Act (CFAA). The use of booter services and stressers also violates this act.Sep 14, 2021