Bypass Proxy For Wifi
F Bypassing a Proxy Server
Users who are granted Administrator access privileges should not connect to the Mobile Server through a proxy server. The Mobile Server will not be able to see the IP addresses of their client machines and, therefore, will not be able to provide them with Administrator-level access.
Administrators who usually connect to the network through a proxy server must bypass the proxy server before connecting to the Mobile Server.
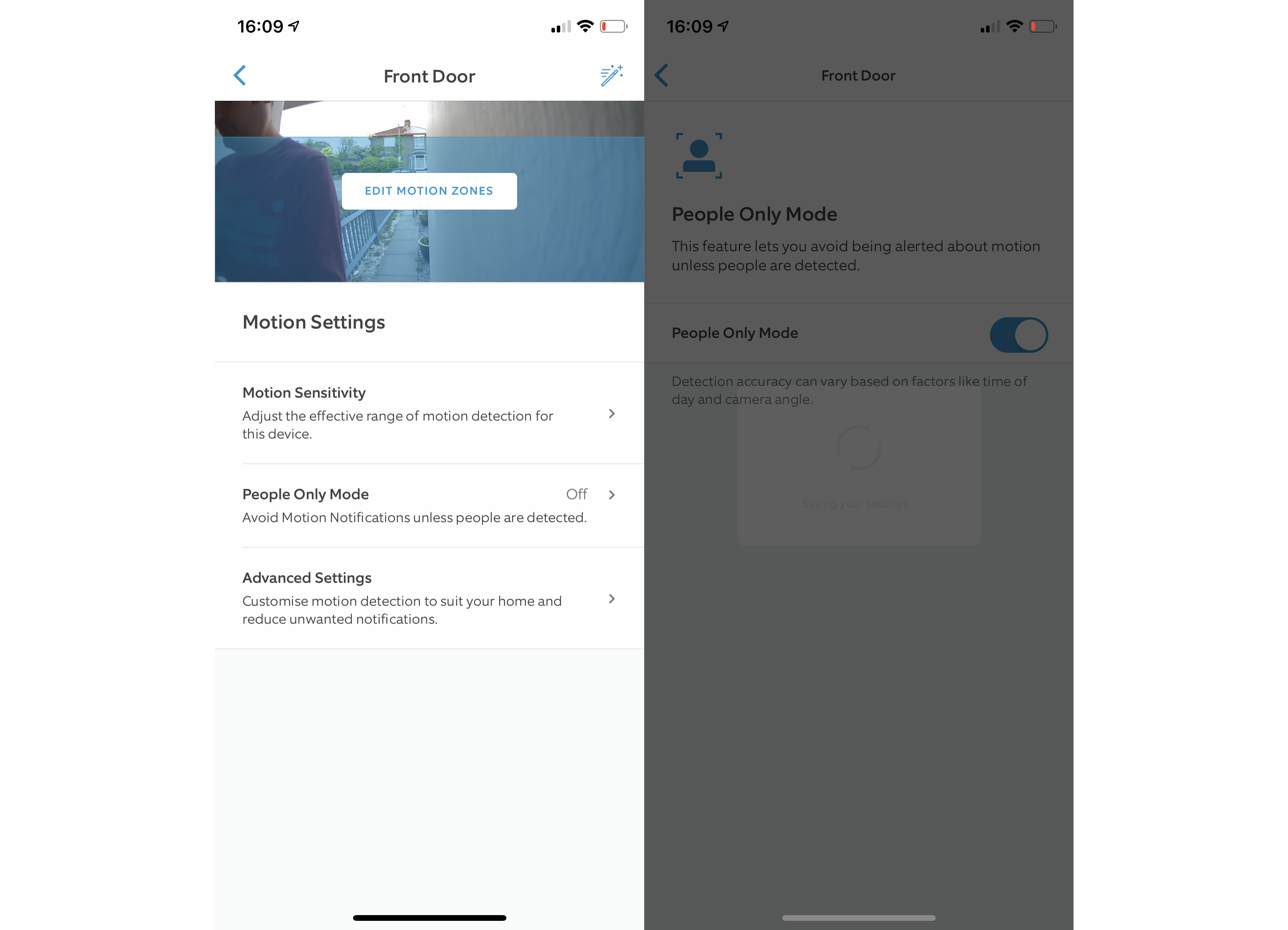
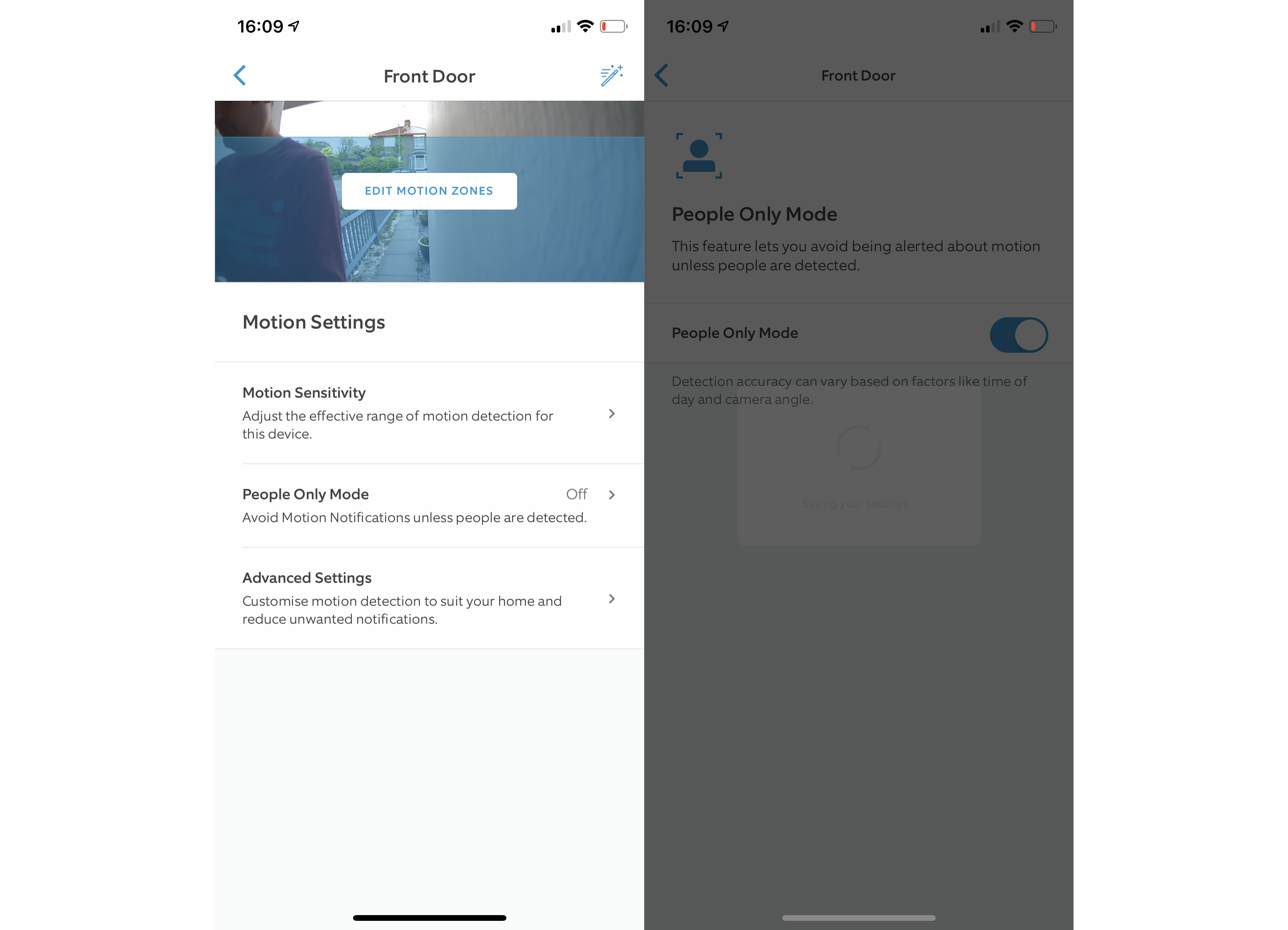
To configure the client machine to bypass a proxy server, perform the following steps.
Double-click the Internet Explorer icon on your desktop and select Internet Options from the Tools menu. The browser displays the Internet Options dialog box.
Click the Connections tab.
Figure F-1 displays the Connection tab.
Figure F-1 Connection Tab – Internet Explorer
Click LAN Settings. Internet Explorer displays the Local Area (LAN) Network Settings dialog.
Figure F-2 displays the Local Area (LAN) Network Settings dialog.
Figure F-2 Local Area Network Settings Dialog
Select the Bypass Proxy Server for Local Addresses check box.
Click Advanced. The Proxy Settings dialog appears.
Figure F-3 displays the Proxy Settings dialog.
Figure F-3 Proxy Settings Dialog
In the Exceptions section, in the field under Do not use proxy server for addresses beginning with:, enter the IP addresses of client machines for user accounts that have Administrator access.
Click OK.
Adding and importing sites that bypass the proxy – Forcepoint
The Proxy Bypass tab of the Bypass Settings page enables you to define sites that bypass the cloud service for all policies. This may include, for example, internal sites that are not accessible from the Internet, so the cloud service cannot serve or analyze them.
Note
The URLs included in the bypass list for Office 365 are those domains that are owned by Microsoft and used directly by the Office 365 application, listed here:
This list also includes third-party URLs that host Certificate Revocation Lists (CRLs), which are not included in the bypass when you select the Office 365 checkbox. Bypassing these domains may not be appropriate for all customers.
If you have difficulty installing or using Office 365 with this option selected, you may need to add one or more of these additional URLs as non-proxied domains. If you need further assistance, please contact Technical Support.
2.
Enter a Name and helpful Description for the destination.
3.
Specify the destination Type, then enter the Address (single IP address), Subnet (using CIDR notation or subnet mask), or Domain.
5.
Use the optional Comment box to add helpful information, such as why the entry was created.
1.
Click Import Destinations.
You can add a total of 1000 proxy bypass destinations per policy. Account-level bypass destinations (added via Web > Proxy Bypass) count towards this limit for each policy. For example, if your policy has 10 bypass destinations, and you have 10 account-level bypass destinations, this is counted as a total of 20 destinations for the policy.

Enter proxy server settings on Mac – Apple Support
Выберите версию:
При изменении этого элемента управления страница автоматически обновится
Если компьютер подключен к локальной сети, защищенной от Интернета брандмауэром, Вам может потребоваться указать настройки прокси-серверов или выбрать пассивный режим FTP (PASV) для доступа к некоторым веб-сайтам. Прокси-сервер — это компьютер в локальной сети, который выступает в качестве посредника между пользователем компьютера и Интернетом, обеспечивая безопасность сети, административный контроль и кэширование. Также можно установить обход настроек прокси для определенных компьютеров в Интернете (хостов) и сегментов Интернета (доменов), добавив адрес хоста или домена в поле «Не использовать прокси для следующих узлов и доменов». Используйте данную функцию, если Вы хотите убедиться в том, что Вы получаете информацию непосредственно с хоста или домена, а не информацию, которая находится в кэш-памяти прокси-сервера. Чтобы обойти один домен, введите доменное имя, например «». Чтобы обойти все веб-сайты домена, используйте знак звездочки перед доменным именем, например «*». Чтобы обойти определенную часть домена, укажите каждую часть, например «».
Максимальное количество символов:
250
Не указывайте в комментарии личную информацию. Максимальное количество символов: 250.
Благодарим вас за отзыв.
Frequently Asked Questions about bypass proxy for wifi
What is a bypass proxy?
The Proxy Bypass tab of the Bypass Settings page enables you to define sites that bypass the cloud service for all policies. … A proxy bypass destination can be a domain name, an IP address, or a subnet. Both the Proxy Connect and Direct Connect endpoint clients use the bypass definitions.
What is proxy server for WiFi?
A proxy server is a computer on a local network that acts as an intermediary between a single computer user and the internet so that the network can ensure security, administrative control, and caching service.
Can hackers bypass proxy servers?
To bypass these proxies, attackers can rely on non-standard ports or tunneling tricks, or they can attack the proxy server itself. Historically, some proxy technologies have suffered from configuration errors or buffer-overflow conditions.
