
Without Ip Address
The MegaNet: How an Internet Without IP Addresses Would …
The Internet is without a doubt one of the most important inventions in modern history. Never before have we had unfettered access to the wealth of the world’s knowledge with just a few keystrokes.
It’s also a flawed vehicle that’s ripe for corruption, and Kim Dotcom hopes to change all that.
According to him, MegaNet will be a newer, better version of the same Internet we all know and love. It’ll feature heavy end-to-end encryption, no IP addresses, and a decentralized structure that makes operation a “for the people, by the people” proposition rather than relying on gatekeepers and government regulation.
It’s ambitious, to say the least.
What Is MegaNet?
In short, the plan for MegaNet is an Internet that’s free from government rule, hackers, and those looking to exploit the massive amounts of data we all leave behind on the Web as we use it. To get there, Dotcom plans to use a lot of technology that we’re already using, most notably: smartphones.
The plan involves using the collective processing power, storage, and bandwidth of hundreds of millions of smartphone users. Each user will donate data to be consumed during those idle periods when they aren’t using it — while they’re sleeping, for example. This data will then be pooled to create the resources needed to send and store files from all corners of the globe.
It’s a similar concept to how a botnet works, except without all of the malice.
MegaNet is intended to be safer for its users by making heavy use of encryption to keep data packets secure from prying eyes. This would prevent the increasingly common data leaks — often including credit card and bank account info — that plague the Web today.
MegaNet will also rely on the blockchain, which is a public ledger that records and stores Bitcoin transactions. Instead of Bitcoin transactions, however, this modified version of the blockchain would store files so that they’re accessible at all times without relying on the traditional server technology we use today.
Instead, chunks of data that make up the Internet — or more accurately, the MegaNet — would be distributed across the globe and then accessed directly from your device.
To keep the MegaNet online at all times — in case the user hosting the file is offline when you attempt to access it — these files would be spread across the globe and multiple users would host each file, or at least pieces of each file.
Why Is MegaNet Even Necessary?
Anecdotally, I think we’re all feeling the pinch of data breaches and government spying.
But if we look at qualitative means, such as this survey by NCC Group [Broken URL Removed], we’ll see that 77 percent of online shoppers don’t feel completely confident that they won’t be part of a data breach, 62 percent are more concerned with online security than they’ve ever been, and 64 percent believe that they’ll be the victim of a breach in the next twelve months.
Not only that, but almost 40 percent of Americans are “very concerned” or “somewhat concerned” about government monitoring of online traffic, according to Pew Research. A nearly identical number expressed concern about government monitoring of their cell phone activity.
Privacy aside, there’s also a really big elephant in the room that nobody seems to want to address: who actually controls the Internet? While there isn’t a governing body, per se, the U. S. Government has taken it upon itself in recent years to police the Internet — and not just in the United States.
Kim Dotcom has firsthand experience with this, as he’s currently awaiting an appeal after being cleared for extradition to the United States to stand trial for federal racketeering, money laundering, and copyright infringement charges.
Aside from the Dotcom example, the U. Government was also the most integral influence in Sweden’s — a country with notoriously lax copyright [Broken URL Removed] laws — decision to send Pirate Bay co-founders Frederik Neij, Gottfrid Svartholm, and Peter Sunde to prison for facilitating copyright infringement through their popular torrent site.
Ultimately, MegaNet isn’t just about security and privacy from hackers and the prying eyes of the government. It’s about creating an Internet that’s virtually untouchable. Without IP addresses, individuals and websites can’t be hacked. You can’t run DDoS attacks. You can’t pull websites down for violations of the laws of any single governing body.
MegaNet is about freedom and transparency, things the Internet was praised for at inception but seems poised to lose as its foundation crumbles under the weight of it all.
Can MegaNet Actually Happen?
Yes, but it probably won’t, at least as Dotcom currently describes it.
The Internet is constantly evolving. We’ve moved from HTTP to HTTPS in recent years to shore up security through better encryption. We’re in the process of switching from IPv4 to IPv6 to provide more IP addresses. We’re debating appropriate levels of privacy versus loss of liberty.
We’re still in the infancy stages of the Internet, and it’s only natural that it continues to grow and adapt to the changing needs of its users.
Dotcom’s service has a number of problems, not the least of which is the fact that he could be facing a lengthy prison sentence in the United States should he lose his appeal. Another roadblock to consider is government interference, which could grind the whole process to a halt by outlawing the technologies that the service is built upon.
So far, tethering hundreds of millions of cell phones, building in safeguards that prevent government intrusion, and anonymizing currency transfers through use of the blockchain are all in a legal gray area. Any or all of these could be banned, which would effectively end MegaNet before it ever built up the steam it needs to take off.
Speaking of taking off, that’s another major flaw in the theory. In order to reach critical mass, MegaNet needs a staggeringly high number of users to make this even feasible. Dotcom says he predicts 100 million users will sign up in the first year. As astronomical as that number seems, it’s not even clear if that would be enough to avoid major bottlenecks.
MegaNet, it appears, might be far before its time. In order to execute something at this grand a scale, you need one of two things to happen:
A good deal of the world’s population to be contributing resources via smartphone data.
Technology to improve.
We’re certain of number two, but the adoption numbers strike me as, well, optimistic. I wouldn’t argue against a need for this kind of service, but as a tech writer, it’s quite clear that the general public wouldn’t understand this nor have any real inclination as to why it was needed (without a healthy dose of education).
If it were as simple as “this is better than what you’re currently using”, we’d all be using Bitcoin by now, and we all know that isn’t happening any time soon. Consumer education remains a significant hurdle to adoption. With lower adoption numbers, the technology needs to get more sophisticated in order to avoid bottlenecks.
We should also note that this is very much a theoretical proposition at this point. The science checks out, the technology is available, and Web users are more security-conscious than ever, but changing consumer behaviors is a tricky proposition.
Dotcom and his team have their work cut out for them, but we’ll get our first glimpse of MegaNet at some point in 2016.
What do you think of a private Internet without IP addresses? Would you use it?
Image Credit: Kim Dotcom addresses the crowd by Peter Harrison via Flickr
Delete These Windows Files and Folders to Free Up Disk SpaceNeed to clear disk space on your Windows computer? Here are the Windows files and folders that can be safely deleted to free up disk space.
Read Next
About The Author
Bryan Clark
(67 Articles Published)
Bryan is a US-born expat currently living on the sunny Baja Peninsula in Mexico. He enjoys science, tech, gadgets, and quoting Will Ferrel movies.
More
From Bryan Clark
Subscribe to our newsletter
Join our newsletter for tech tips, reviews, free ebooks, and exclusive deals!
Click here to subscribe
How to Hide My IP Address – TheBestVPN.com
Hiding an IP address is quite simple if you know which tools to use.
If you’re like me, someone who wants to hide my ip in order to get access to geo-blocked sites, negate IP bans and just stay anonymous, keep reading.
Below, I’ve listed 6 fool-proof ways to hide your IP address including keeping your Internet connection encrypted and fully anonymous.
What is an IP Address?
Let’s first get some basics out of the way.
The internet, being nothing more than a vast group of interconnected networks, requires a system to establish communication between these networks. The Internet Protocol, usually referred to as IP, is the principal technology, responsible for this connection. IP is tasked with defining, structuring and delivering information packets from point A to point B.
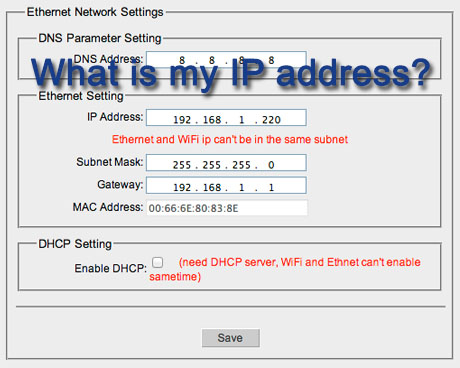
IP addresses are nothing more than system identifiers. In version four of the internet protocol (IPv4), IP addresses are defined as a 32-bit number; x. x. x where x is a value between 0 and 255.
Here are some valid IP addresses:
123. 45. 67. 89
8. 8. 8 – an IP address assigned to Google
140. 247. 224. 81 – an IP address assigned to Harvard University
Every system, connected to the internet, has its own address; much like the address of your house or the license plate of your car. Every system has to have a unique IP address, assigned to that machine, and that machine only. This means your phone, your laptop, work computer and your printer, all have different IP addresses.
Every participant of the internet has to have an IP address to connect to it.
The way IP operates, IP addresses are a sensitive piece of information as they pinpoint the location of the systems they are assigned to. This is uncircumventable, as the physical location of the connected machine is precisely the information necessary for the internet protocol to establish the most efficient connection.
This is how I know that any IP, which starts with 140. 247 will be assigned to Harvard University and how I know where you are based in, simply by looking at your IP address.
6 Ways to Hide Your IP Address
Check out these six ways to alter your IP address.
1. Get a VPN Software
Probably the best and most convenient way for changing your IP is to choose a good VPN service.
Here’s what VPN does:
Hide’s your IP address
Encrypts your internet traffic
Allows you safely torrent
Allows you to get access to geo-blocked sites like Netflix and Hulu.
As you can see, the benefits of a Virtual Private Network are precisely the same as the benefits of changing your IP address.
No surprise here; VPNs assign new IP address to systems connected to them. As you connect to a virtual network, you’ll be assigned a second IP address, which spoofs your real one.
Setting up your VPN client takes minutes, and once you’re all set up, connecting to it and thereby changing your IP happens at the click of your button.
“That’s all great, Andrey, but how does a VPN change my IP address? ”
Great question – I’m excited to tell you.
While you’re connected to a VPN, the VPN provider will assign you a virtual IP address. While your real IP address will still be used to connect to said VPN, all other traffic will be tunneled through your private network and as such this external traffic will only connect to your second, virtual IP address.
I’m recommending NordVPN ($3. 49/mo) because it’s by far the most anonymous and reliable VPN software we’ve tested to date. It’s secure and it doesn’t like your IP address. You can choose from their 1500+ servers (different IP’s). You can read our NordVPN review here.
Another good VPN service option (at a cheaper cost) is Surfshark ($1. 99/mo) Read our Surfshark review here.
ExpressVPN is also an option, but it comes at a higher price point. ($6. 67/mo). Read our ExpressVPN review here.
2. Use a Proxy – Slower than VPN
Proxy servers are great little tools which act as a bridge in the flow of your internet traffic. These man-in-the-middle servers connect your information packets to their desired destination while changing their appearance as they go through the Proxy.
In simpler terms, the Proxy server intercepts your traffic and takes control of your connection. From here, everything you do, the proxy server repeats; it mirrors your behavior. The destination servers (websites you’d like to access) think of the proxy is your traffic.
The beauty of this system is that you can connect to any proxy server in the world.
Say you want to access UK’s BBC. You’ll quickly find out that most of their content is blocked and inaccessible for people outside the United Kingdom. In comes the Proxy server. You connect to a UK based Proxy and voila – for all intents and purposes, you’re henceforth as British as fish and chips.
Proxy servers are very efficient at low profile necessities such as bypassing geo-blocked content or IP restrictions.
Being able to mask your real IP address is where the similarities between VPNs and Proxies end.
While being more than adept at handling Netflix geo-restricted content, Proxies can’t compete with a VPN’s many layers of security. Outside spoofing your IP address, Proxy servers neither encrypt your data nor remove any identifiable markers from it. Proxies will do nothing to shield you from the prying eyes of your ISP, government or anyone with access to your data.
The final big difference between Proxies and VPNs is the former’s lack of encompassing spoofing. While a VPN will encrypt any and all data coming into and out of your system, a Proxy will intercept traffic on a per-application basis.
Say you connect your web browser to a proxy server. Great! You can watch all the Netflix you want, don’t go torrenting files, however. Your torrenting traffic won’t be intercepted by your Proxy and your ISP can easily see what you’re up to.
Further reading: Difference between VPN and Proxy
3. Use TOR – FREE
TOR, named after the original project “The Onion Router” is a free client which anonymously connects you to volunteer-operated network of servers. This enables you to be assigned a new IP address, on the same basis as a VPN client.
Also known as the “dark/deep” web, Tor has the added benefit of enabling you to access websites, otherwise inaccessible with normal browsers. Such “onion” websites have very different domain names as they are mostly randomly generated.
Check out the domain name of the anonymity search engine DuckDuckGo:
TOR being a widely accessible, free and anonymous network, it has become a hub for criminal activity. Also one of the reasons why you may be put on a “list” if you access TOR, a big chunk of the network’s users connect to it to carry out illegal transactions. From false identities to heavy drugs and even weaponry.
Another big drawback of TOR is the extremely slow loading times. These long loading times are predicated on the inefficient and long-winded routes that your data packets are sent on, relayed from server to server, until they finally hit their destination. This, of course, is all done in the name of safety.
Make no mistake, TOR isn’t entirely foolproof. Certain software vulnerabilities and website admin errors can and are exploited by Government agency.
Further reading: Tor vs. VPN (What is the difference)
4. Use Mobile Network – Slow and not encrypted
A quick way to change your IP address, if you fear yours has been compromised, is to use your cell phone’s data. As it’s a different system, it will have a different IP address.
This, of course, is no substitute to a laptop/PC workstation. It may aid you in rare emergency situations, when your IP is obviously being attacked, but outside of that, relying on Mobile Data is both ineffective and short-sighted.
5. Connect to Public Wi-Fi – Not Secure
As IP addresses don’t travel with you, using your laptop to connect to a coffee shop’s open Wi-Fi network is an easy way to change your IP address. Same as with Mobile Data, this is neither an effective IP change method, nor a sustainable way of surfing anonymously & securely.
Unfortunately, there are many risks when using such open hotspots networks.
6. Call Your Internet Service Provider
The bitter truth is that we have zero influence on what IP address our systems get assigned to. We can only ask or force our Internet Service Providers to change our IPs for us.
There are two types of IP addresses that your ISP will assign to you. Static and Dynamic. A static IP is difficult to change as you’ll have to go through a lengthy process with your ISP. Most internet providers will, fortunately, assign dynamic IPs.
Asking nicely, so Mom thought me, is always step one. Calling up your ISP and simply asking for an IP change will often do the trick, though you may have to face some unexpected and forward questions as to your motivation behind such a request. Telling them you’re teaching son or younger brother the basics of networking, seems to do the trick.
Force an IP change by unplugging your modem
If being nice fails, an easy way to attempt to force an IP change by your ISP, is to unhook your modem and reconnect it after a little while. By severing your connection to your ISP, you’re very likely to be assigned a new IP range. This only works if you operate on dynamic IPs, however. You also have to remain disconnected from the internet for many hours to prompt a change in IP address.
Here are some additional steps you can take on Windows before unhooking your Modem:
Windows system connected via cable
Open Command Prompt as Administrator
Type “ipconfig /release“, without the quotes and hit Enter
Type “ipconfig /renew“, without the quotes and hit Enter
Shut down your system.
Turn off all ethernet hubs/switches.
Unplug cable/DSL modem.
Leave off as long as you can bare (overnight)
Turn everything back on.
Windows system connected via router
Log into the router’s admin console.
Release the IP address (Every router is different, Google yours)
Are you chuckling yet? I sure am
I’m not saying the above doesn’t work – it works just fine. I’m saying I’m not about to dial my phone and sit on hold for half an hour or disconnect myself from the internet every time I want to change my IP address.
With ISP’s selling my browsing history to the highest bidder, I sure wouldn’t trust them to help me out either.
Effective? Yes! Practical? Heck No!
Unfortunately for you and me, this about sums up the ways we can change our IP address. Sure, there are others, more technical ones. If you’re an expert in networking you can modify your router and force a dynamic IP change that way – but that’s neither simple, nor quick, nor guaranteed.
Changing IP addresses simply isn’t the way to go, hiding them, however, is another story entirely
Why Hide IP?
It is very much in our interest to make sure no wrong-doers ever get their hands on such an important identifier as our IP Address. Let’s take a look at the main reasons why you would want to hide your IP address.
1. Hide Your Location
As mentioned above, your IP address functions much like the street address of your home; it tells the Internet Protocol where to send your requested information packets. This is predicated on the IP’s ability to pinpoint your exact location, enabling it to connect you to your nearest network and from there to the world.
Here is a list of geo-location information that your IP address harbors:
Country
Region
City
ZIP code
Longitude and latitude
Pretty scary to think that a criminal could have access to your GPS coordinates by simply finding out your IP, isn’t it?
2. Circumvent IP restrictions
Being a very precise location identifier, your IP address is often used to block you from accessing certain information which someone has deemed inaccessible for you.
When governments like those in China, Russia and, Yes, the United States restrict access to certain websites and services by blocking their nation’s IP addresses, “spoofing, the act of masking your IP address, comes in handy.
From journalists to activists and your everyday person, nobody should be oppressed and restricted to share their views in the information era.
Colleges and universities also love to meddle with their student’s internet access. Many schools have banned online video game servers from being accessed. This means no League of Legends, World of Warcraft, CS:GO and so on.
I guess these students are mature enough to rack up $200K in debt for a four-year degree, but giving them access to online games? That’s too much.
Circumventing such IP restrictions is important to make sure you, and only you, get to decide which content you’d like to access.
3. Negate IP Bans
Banning your IP address is an easy way for websites and services to immediately block your access to them. This quickly becomes a problem as you try to connect to your paid-for Netflix account, a service which blocks any and all IPs outside the USA from accessing their US library of moves and TV shows, when you’re sitting in your hotel room overseas.
Spoofing or changing your IP address is a quick and easy way of loopholing your way back into services you’ve been mistakenly or unjustly banned from.
4. Block Targeted Attacks
Hiding your IP address quickly becomes a must-do security step once you’ve been targeted by a cyber-criminal, who is after your personal records.
By changing your vulnerable IP address you can throw off and block this specific type of cyber attack on your system.
5. Remain Anonymous on Internet
Anonymity is to be expected, not asked for. Well, not anymore.
When our Congress passes bills, allowing Internet Service Providers to sell your private web surfing data & browsing history to the highest bidder, retaining anonymity in an ever-shrinking world seems all the more precious and important.
Conclusion
Changing your IP address is one of many security steps as you embark on the journey of securing yourself and your data. While there are more comprehensive ways of protection, such as using a VPN, I commend you on your desire and prudence to seek out ways to shield your IP address from hackers and no-gooders.
I sincerely hope this article has helped you find your preferred method of keeping your IP address safe on the inter-webs. Please share it with your friends and colleagues and let me know about your experiences with IP addresses.
Time to drop the mic, you made it!
Surf Safe,
Andrey from team
What is an IP Address – Definition and Explanation – Kaspersky
IP address definition
An IP address is a unique address that identifies a device on the internet or a local network. IP stands for “Internet Protocol, ” which is the set of rules governing the format of data sent via the internet or local network.
In essence, IP addresses are the identifier that allows information to be sent between devices on a network: they contain location information and make devices accessible for communication. The internet needs a way to differentiate between different computers, routers, and websites. IP addresses provide a way of doing so and form an essential part of how the internet works.
What is an IP?
An IP address is a string of numbers separated by periods. IP addresses are expressed as a set of four numbers — an example address might be 192. 158. 1. 38. Each number in the set can range from 0 to 255. So, the full IP addressing range goes from 0. 0. 0 to 255. 255. 255.
IP addresses are not random. They are mathematically produced and allocated by the Internet Assigned Numbers Authority (IANA), a division of the Internet Corporation for Assigned Names and Numbers (ICANN). ICANN is a non-profit organization that was established in the United States in 1998 to help maintain the security of the internet and allow it to be usable by all. Each time anyone registers a domain on the internet, they go through a domain name registrar, who pays a small fee to ICANN to register the domain.
How do IP addresses work
If you want to understand why a particular device is not connecting in the way you would expect or you want to troubleshoot why your network may not be working, it helps understand how IP addresses work.
Internet Protocol works the same way as any other language, by communicating using set guidelines to pass information. All devices find, send, and exchange information with other connected devices using this protocol. By speaking the same language, any computer in any location can talk to one another.
The use of IP addresses typically happens behind the scenes. The process works like this:
Your device indirectly connects to the internet by connecting at first to a network connected to the internet, which then grants your device access to the internet.
When you are at home, that network will probably be your Internet Service Provider (ISP). At work, it will be your company network.
Your IP address is assigned to your device by your ISP.
Your internet activity goes through the ISP, and they route it back to you, using your IP address. Since they are giving you access to the internet, it is their role to assign an IP address to your device.
However, your IP address can change. For example, turning your modem or router on or off can change it. Or you can contact your ISP, and they can change it for you.
When you are out and about – for example, traveling – and you take your device with you, your home IP address does not come with you. This is because you will be using another network (Wi-Fi at a hotel, airport, or coffee shop, etc. ) to access the internet and will be using a different (and temporary) IP address, assigned to you by the ISP of the hotel, airport or coffee shop.
As the process implies, there are different types of IP addresses, which we explore below.
Types of IP addresses
There are different categories of IP addresses, and within each category, different types.
Consumer IP addresses
Every individual or business with an internet service plan will have two types of IP addresses: their private IP addresses and their public IP address. The terms public and private relate to the network location — that is, a private IP address is used inside a network, while a public one is used outside a network.
Private IP addresses
Every device that connects to your internet network has a private IP address. This includes computers, smartphones, and tablets but also any Bluetooth-enabled devices like speakers, printers, or smart TVs. With the growing internet of things, the number of private IP addresses you have at home is probably growing. Your router needs a way to identify these items separately, and many items need a way to recognize each other. Therefore, your router generates private IP addresses that are unique identifiers for each device that differentiate them on the network.
Public IP addresses
A public IP address is the primary address associated with your whole network. While each connected device has its own IP address, they are also included within the main IP address for your network. As described above, your public IP address is provided to your router by your ISP. Typically, ISPs have a large pool of IP addresses that they distribute to their customers. Your public IP address is the address that all the devices outside your internet network will use to recognize your network.
Public IP addresses come in two forms – dynamic and static.
Dynamic IP addresses
Dynamic IP addresses change automatically and regularly. ISPs buy a large pool of IP addresses and assign them automatically to their customers. Periodically, they re-assign them and put the older IP addresses back into the pool to be used for other customers. The rationale for this approach is to generate cost savings for the ISP. Automating the regular movement of IP addresses means they don’t have to carry out specific actions to re-establish a customer’s IP address if they move home, for example. There are security benefits, too, because a changing IP address makes it harder for criminals to hack into your network interface.
Static IP addresses
In contrast to dynamic IP addresses, static addresses remain consistent. Once the network assigns an IP address, it remains the same. Most individuals and businesses do not need a static IP address, but for businesses that plan to host their own server, it is crucial to have one. This is because a static IP address ensures that websites and email addresses tied to it will have a consistent IP address — vital if you want other devices to be able to find them consistently on the web.
This leads to the next point – which is the two types of website IP addresses.
There are two types of website IP addresses
For website owners who don’t host their own server, and instead rely on a web hosting package – which is the case for most websites – there are two types of website IP addresses. These are shared and dedicated.
Shared IP addresses
Websites that rely on shared hosting plans from web hosting providers will typically be one of many websites hosted on the same server. This tends to be the case for individual websites or SME websites, where traffic volumes are manageable, and the sites themselves are limited in terms of the number of pages, etc. Websites hosted in this way will have shared IP addresses.
Dedicated IP addresses
Some web hosting plans have the option to purchase a dedicated IP address (or addresses). This can make obtaining an SSL certificate easier and allows you to run your own File Transfer Protocol (FTP) server. This makes it easier to share and transfer files with multiple people within an organization and allow anonymous FTP sharing options. A dedicated IP address also allows you to access your website using the IP address alone rather than the domain name — useful if you want to build and test it before registering your domain.
How to look up IP addresses
The simplest way to check your router’s public IP address is to search “What is my IP address? ” on Google. Google will show you the answer at the top of the page.
Other websites will show you the same information: they can see your public IP address because, by visiting the site, your router has made a request and therefore revealed the information. The site IPLocation goes further by showing the name of your ISP and your city.
Generally, you will only receive an approximation of location using this technique — where the provider is, but not the actual device location. If you are doing this, remember to log out of your VPN too. Obtaining the actual physical location address for the public IP address usually requires a search warrant to be submitted to the ISP.
Finding your private IP address varies by platform:
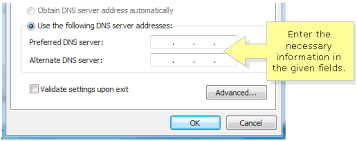
In Windows:
Use the command prompt.
Search for “cmd” (without the quotes) using Windows search
In the resulting pop-up box, type “ipconfig” (no quote marks) to find the information.
On a Mac:
Go to System Preferences
Select network – and the information should be visible.
On an iPhone:
Go to Settings
Select Wi-Fi and click the “i” in a circle () next to the network you are on – the IP address should be visible under the DHCP tab.
If you need to check the IP addresses of other devices on your network, go into the router. How you access the router depends on the brand and the software it uses. Generally, you should be able to type the router’s gateway IP address into a web browser on the same network to access it. From there, you will need to navigate to something like “attached devices, ” which should display a list of all the devices currently or recently attached to the network — including their IP addresses.
IP address security threats
Cybercriminals can use various techniques to obtain your IP address. Two of the most common are social engineering and online stalking.
Attackers can use social engineering to deceive you into revealing your IP address. For example, they can find you through Skype or a similar instant messaging application, which uses IP addresses to communicate. If you chat with strangers using these apps, it is important to note that they can see your IP address. Attackers can use a Skype Resolver tool, where they can find your IP address from your username.
Online stalking
Criminals can track down your IP address by merely stalking your online activity. Any number of online activities can reveal your IP address, from playing video games to commenting on websites and forums.
Once they have your IP address, attackers can go to an IP address tracking website, such as, type it in, and then get an idea of your location. They can then cross-reference other open-source data if they want to validate whether the IP address is associated with you specifically. They can then use LinkedIn, Facebook, or other social networks that show where you live, and then see if that matches the area given.
If a Facebook stalker uses a phishing attack against people with your name to install spying malware, the IP address associated with your system would likely confirm your identity to the stalker.
If cybercriminals know your IP address, they can launch attacks against you or even impersonate you. It is important to be aware of the risks and how to mitigate them. Risks include:
Downloading illegal content using your IP address
Hackers are known to use hacked IP addresses to download illegal content and anything else they do not want to be traced back to them. For example, using the identity of your IP address, criminals could download pirated movies, music, and video – which would breach your ISP’s terms of use – and much more seriously, content related to terrorism or child pornography. This could mean that you – through no fault of your own – could attract the attention of law enforcement.
Tracking down your location
If they know your IP address, hackers can use geolocation technology to identify your region, city, and state. They only need to do a little more digging on social media to identify your home and potentially burgle it when they know you are away.
Directly attacking your network
Criminals can directly target your network and launch a variety of assaults. One of the most popular is a DDoS attack (distributed denial-of-service). This type of cyberattack occurs when hackers use previously infected machines to generate a high volume of requests to flood the targeted system or server. This creates too much traffic for the server to handle, resulting in a disruption of services. Essentially, it shuts down your internet. While this attack is typically launched against businesses and video game services, it can occur against an individual, though this is much less common. Online gamers are at particularly high risk for this, as their screen is visible while streaming (on which an IP address can be discovered).
Hacking into your device
The internet uses ports as well as your IP address to connect. There are thousands of ports for every IP address, and a hacker who knows your IP can try those ports to attempt to force a connection. For example, they could take over your phone and steal your information. If a criminal does obtain access to your device, they could install malware on it.
How to protect and hide your IP address
Hiding your IP address is a way to protect your personal information and online identity. The two primary ways to hide your IP address are:
Using a proxy server
Using a virtual private network (VPN)
A proxy server is an intermediary server through which your traffic is routed:
The internet servers you visit see only the IP address of that proxy server and not your IP address.
When those servers send information back to you, it goes to the proxy server, which then routes it to you.
A drawback of proxy servers is that some of the services can spy on you — so you need to trust it. Depending on which one you use, they can also insert ads into your browser.
VPN offers a better solution:
When you connect your computer – or smartphone or tablet – to a VPN, the device acts as if it is on the same local network as the VPN.
All your network traffic is sent over a secure connection to the VPN.
Because your computer behaves as if it is on the network, you can securely access local network resources even when you are in another country.
You can also use the internet as if you were present at the VPN’s location, which has benefits if you are using public Wi-Fi or want to access geo-blocked websites.
Kaspersky Secure Connection is a VPN that protects you on public Wi-Fi, keeps your communications private, and ensures that you are not exposed to phishing, malware, viruses, and other cyber threats.
When should you use VPN
Using a VPN hides your IP address and redirects your traffic through a separate server, making it much safer for you online. Situations where you might use a VPN include:
When using public Wi-Fi
When using a public Wi-Fi network, even one that is password-protected, a VPN is advisable. If a hacker is on the same Wi-Fi network, it is easy for them to snoop on your data. The basic security that the average public Wi-Fi network employs does not provide robust protection from other users on the same network.
Using a VPN will add an extra layer of security to your data, ensuring you bypass the public Wi-Fi’s ISP and encrypting all your communication.
When you are traveling
If you are traveling to a foreign country – for example, China, where sites like Facebook are blocked – a VPN can help you access services that may not be available in that country.
The VPN will often allow you to use streaming services that you paid for and have access to in your home country, but they are not available in another because of international rights issues. Using a VPN can enable you to use the service as if you were at home. Travelers may also be able to find cheaper airfare when using a VPN, as prices can vary from region to region.
When you are working remotely
This is especially relevant in the post-COVID world, where many people are working remotely. Often employers require the use of a VPN to access company services remotely for security reasons. A VPN that connects to your office’s server can give you access to internal company networks and resources when you are not in the office. It can do the same for your home network while you are out and about.
When you just want some privacy
Even in the comfort of your own home, using the internet for everyday purposes, using a VPN can be a good idea. Whenever you access a website, the server you connect to logs your IP address and attaches it to all the other data the site can learn about you: your browsing habits, what you click on, how long you spend looking at a particular page. They can sell this data to advertising companies who use it to tailor ads straight to you. This is why ads on the internet sometimes feel oddly personal: it’s because they are. Your IP address can also be used to track your location, even when your location services are turned off. Using a VPN prevents you from leaving footprints on the web.
Don’t forget your mobile devices, either. They have IP addresses too, and you probably use them in a wider variety of locations than your home computer, including public Wi-Fi hotspots. It is advisable to use a VPN on your mobile when connecting to a network you may not fully trust.
Other ways to protect your privacy
Change privacy settings on instant messaging applications
Apps installed on your device are a major source of IP address hacking. Instant messaging and other calling apps can be used as a tool by cybercriminals. Using IM apps only allows direct connections from contacts and doesn’t accept calls or messages from people you don’t know. Changing your privacy settings makes it harder to find your IP address because people who don’t know you cannot connect with you.
Create unique passwords
Your device password is the only barrier that can restrict people from accessing your device. Some people prefer to stick to their devices’ default passwords, which makes them vulnerable to attack. Like all your accounts, your device needs to have a unique and strong password that is not easy to decode. A strong password contains a mix of upper- and lower-case letters, numerals, and characters. This will help to safeguard your device against IP address hacking.
Stay alert to phishing emails and malicious content
A high proportion of malware and device tracking software is installed via phishing emails. When you connect with any site, this provides the site with access to your IP address and device location, making it vulnerable to hacking. Be vigilant when opening emails from unknown senders and avoid clicking on links that could send you to unauthorized sites. Pay close attention to the emails’ content, even if they appear to come from well-known sites and legitimate businesses.
Use a good antivirus solution and keep it up to date
Install comprehensive antivirus software and keep it up to date. For example, Kaspersky’s Anti-Virus protection guards you from viruses on your PC and Android devices, secures and stores your passwords and private documents, and encrypts the data you send and receive online with VPN.
Protecting your IP address is a crucial aspect of protecting your online identity. Securing it through these steps is a way to stay safe against the wide variety of cybercriminals’ attacks.
Related articles:
How safe are smart homes
Internet of Things security threats
What is IP spoofing and how to prevent it
What is Voice Over IP (VOIP)
Tips to protect yourself from cyberstalkers
Frequently Asked Questions about without ip address
Can I use Internet without IP address?
Without IP addresses, individuals and websites can’t be hacked. You can’t run DDoS attacks. You can’t pull websites down for violations of the laws of any single governing body.Jan 20, 2016
How can I use without IP address?
6 Ways to Hide Your IP AddressGet a VPN Software. Probably the best and most convenient way for changing your IP is to choose a good VPN service. … Use a Proxy – Slower than VPN. … Use TOR – FREE. … Use Mobile Network – Slow and not encrypted. … Connect to Public Wi-Fi – Not Secure. … Call Your Internet Service Provider.Mar 15, 2019
Is an IP address necessary?
The internet needs a way to differentiate between different computers, routers, and websites. IP addresses provide a way of doing so and form an essential part of how the internet works.

